How will attackers respond to Mythos?
A look at the ways AI‑driven vulnerability discovery will reshape CVE trends and attacker behavior
Takeaways
- AI will create a surge in the number of disclosed CVEs before stabilizing at a lower baseline of exploitable flaws.
- Attackers will prioritize targets with slower AI adoption and patching timelines.
- Patch releases will accelerate exploit development, as attackers use ‘patch‑diff’ engineering to identify what was changed and target unpatched systems.
| From the desk of the CISO is authored by Arve Kjoelen, Chief Information Security Officer (CISO) at Barracuda. It examines the strategic implications of emerging security trends — not just the technical mechanics behind them. It is written for IT and security leaders who need to understand what is changing, why it matters and where to focus next — often before there is clear industry consensus. |
As software vendors scan their code with Mythos and other large language models (LLMs), they will publish new Common Vulnerabilities and Exposures (CVEs) for vulnerabilities found in their existing software. This will create a surge in the number of disclosed CVEs. However, vendors’ new software is likely to contain fewer vulnerabilities because it has been scanned with LLMs before release. This trend will be more pronounced for companies using LLMs aggressively and less pronounced for companies in the experimentation phase or using less powerful models.
The CVE bubble is coming, and attacker‑exploited vulnerabilities will make up a larger share once it stabilizes. Whether the bubble lasts one year or longer is uncertain. But attackers who understand these trends will begin preparing now.
Here’s how I believe the attackers will react to vendor behavior:
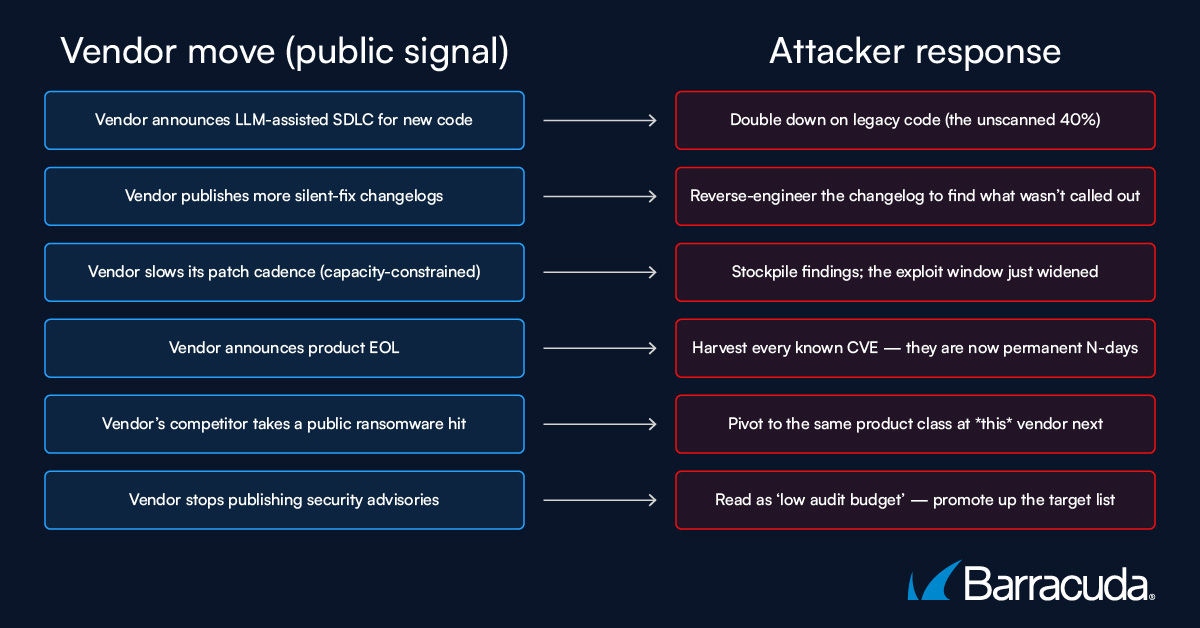
Public vendor actions and the corresponding attacker playbook, including reverse engineering, exploit development and target reprioritization
What will attackers do in response?
I predict attackers will increasingly segment their treatment of software vendors to maximize their own economic benefit:
Group 1 – Soft prime targets: These vendors have attractive products but slow artificial intelligence (AI) adoption. Attackers will continue targeting them using current tactics augmented with AI.
Group 2 – Large vendors who quickly adopt AI for vulnerability discovery: As these vendors issue patches, attackers will continue using patch‑diff engineering — analyzing changes between vulnerable and patched versions — to create exploits.
Group 3 – Lower-value vendors slow to adopt AI: Attackers will target these vendors opportunistically, sitting on discovered vulnerabilities until an opportune time.
Group 4 – Lower-value vendors rapidly adopting AI: Attackers are likely to skip these vendors.
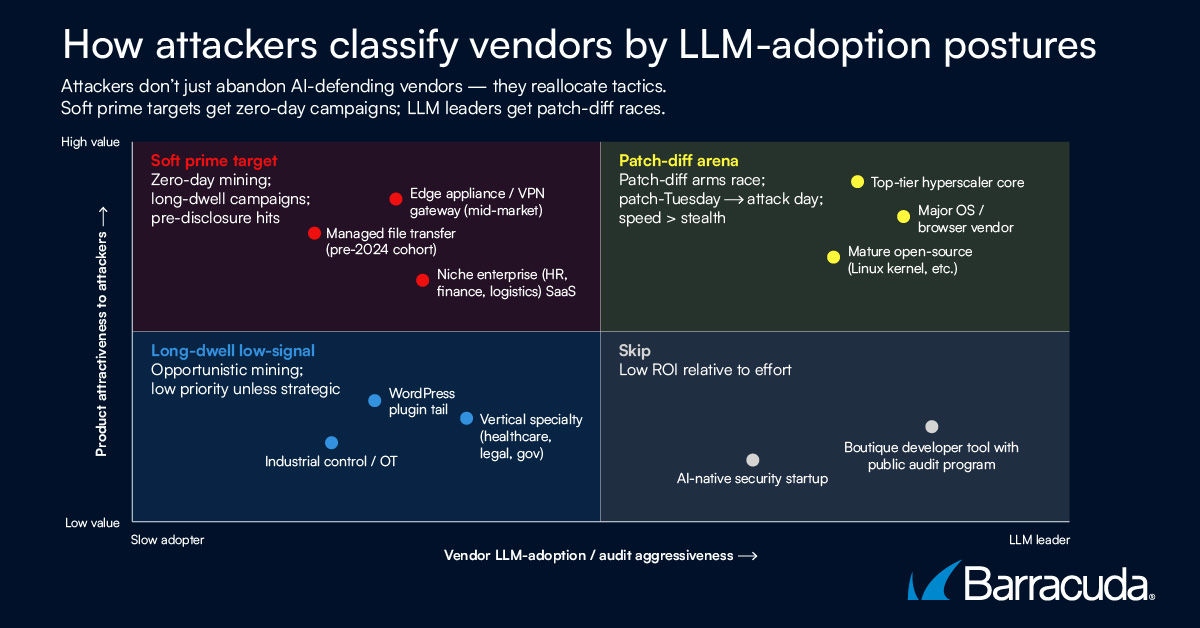
Although no vendor is safe, the most exposed vendors will be those slow to adopt LLM-scanning of their code. Further analysis is available at our AI Hype site.
This presents a grave challenge for software vendors and end users. My next article will look at recommendations and unorthodox options for response.

2026 Email Threats Report
Learn how AI and phishing-as-a-service are reshaping the email threat landscape and how to stay protected
Subscribe to the Barracuda Blog.
Sign up to receive threat spotlights, industry commentary, and more.
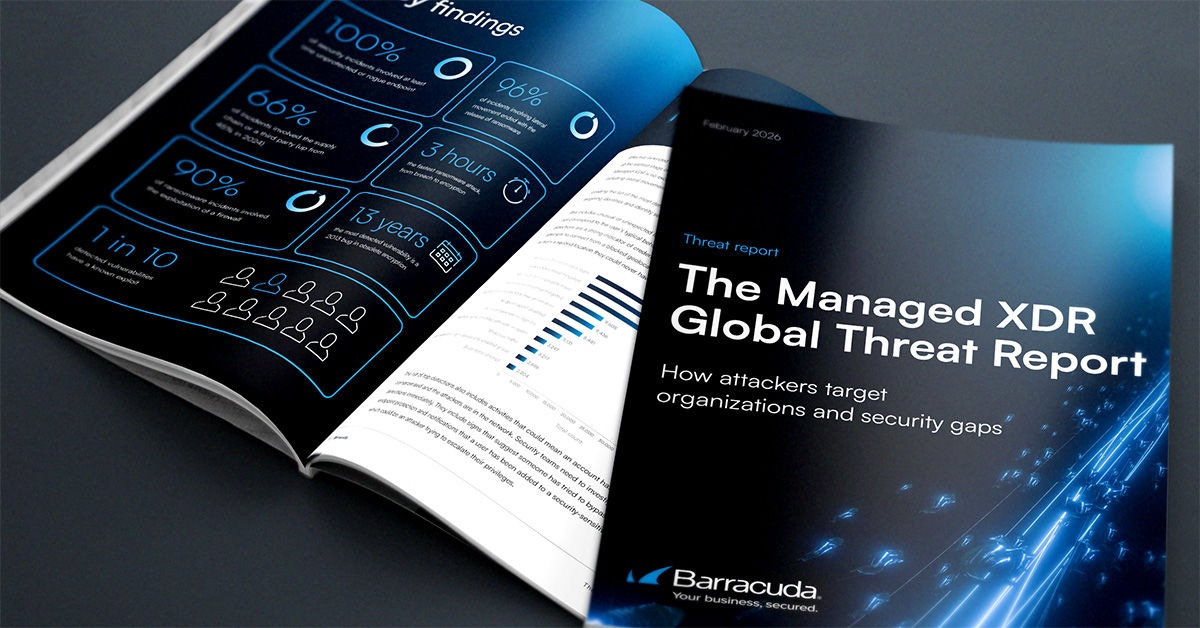
The Managed XDR Global Threat Report
Key findings about the tactics attackers use to target organizations and the security weak spots they try to exploit