Threat Spotlight: Boutique phishing kit Saiga 2FA hides behind ‘lorem ipsum’ metadata
Rarely seen configurable phishing kit runs highly targeted campaigns
Takeaways
- Saiga 2FA is a little seen, small-scale but sophisticated phishing kit.
- Barracuda attack flow analysis reveals evasion and runtime configurability.
- Analysis underscores importance of phishing-resistant authentication and URL verification.
In early 2025, a sophisticated phishing kit, Saiga 2FA, was seen targeting legal organizations in Australia. Since then, the kit has stayed largely under the radar. New Barracuda detection data shows that its activity has ramped up in recent months, with a significant wave of phishing campaigns beginning in February 2026.
Saiga 2FA belongs to a class of advanced phishing kits that function more like a boutique service than an automated platform. It features a structured, modular and infrastructure-driven design.
This article examines the attack flow, tools and techniques seen by Barracuda threat analysts in Saiga’s recent campaign.
The Saiga attack flow
Like other phishing kits, Saiga uses an adversary-in-the-middle (AitM) approach to bypass multifactor authentication, stealing session cookies in real time.
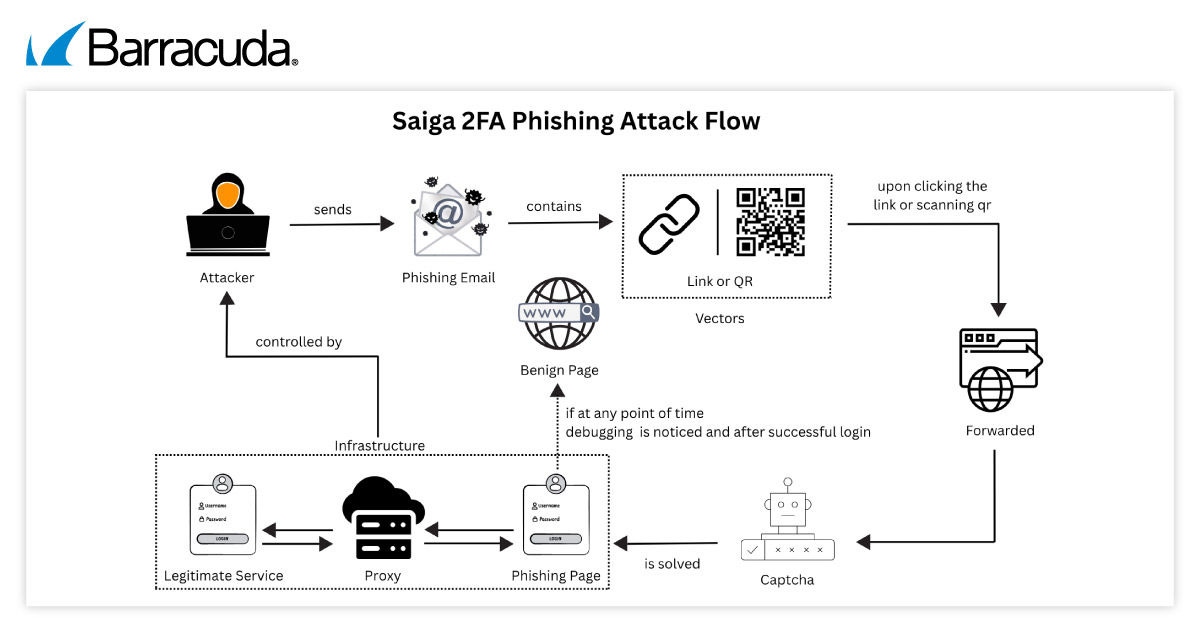
Saiga 2FA Phishing Attack Flow. AI-generated illustration for educational purposes.
Initial access
The phishing campaign analyzed by Barracuda typically starts with phishing emails impersonating Docusign notifications and asking the recipient to review or sign the document.
The lure is crafted to appear urgent and legitimate. In several cases, the link is embedded directly in the email body, while in others, a QR code is used to redirect victims to the phishing infrastructure.
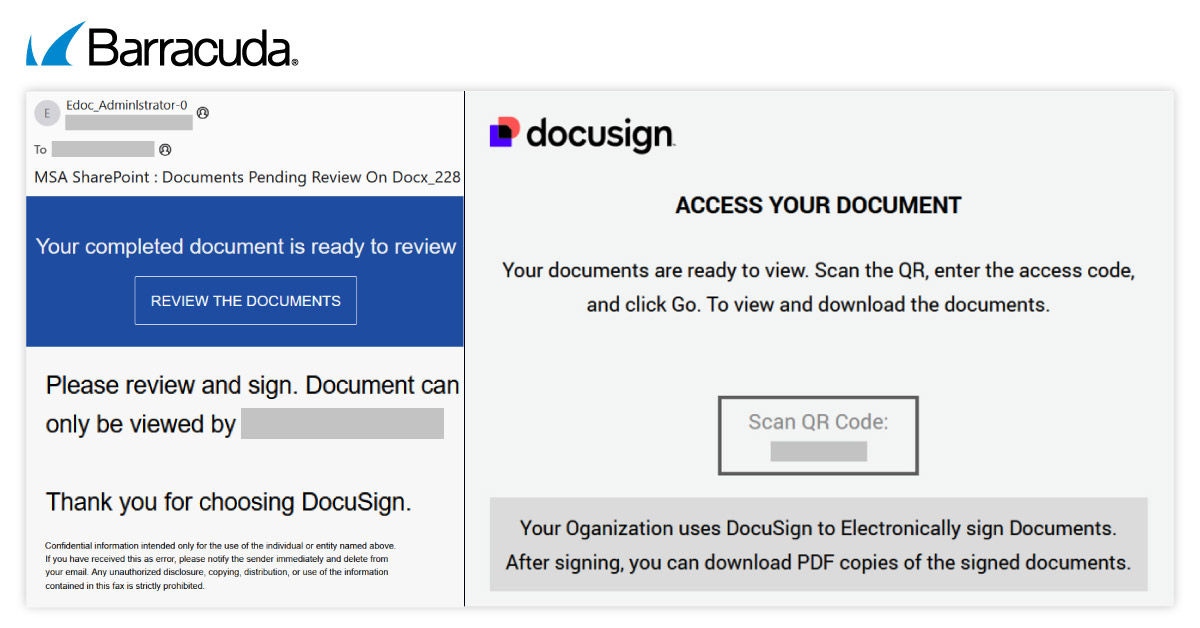
Saiga 2FA Phishing Kit lure
Once the recipient clicks the link, the resulting redirection chain wraps reputable URL protection services and tracking links round the web address to ensure it looks safe and legitimate and can continue unimpeded to the final phishing domain.
Evasion techniques
Like other phishing kits, Saiga 2FA employs multiple, layered evasion techniques to reduce detection and hinder analysis — although it can take an original approach to achieving this.
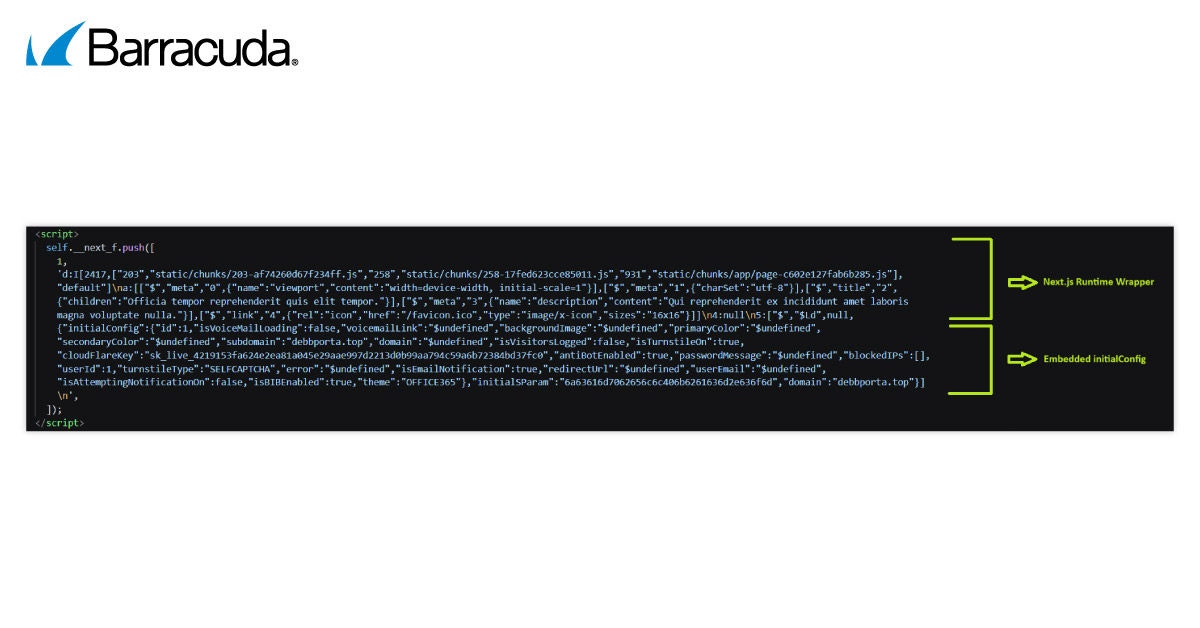
1. Placeholder metadata (lorem ipsum)
Instead of using familiar, user-trusted titles such as ‘Microsoft Login,’ ‘Adobe Sign In’ or ‘Authenticating …’ (as used by the phishing kit, Mamba 2FA), or the more technical ‘​’ (associated with Tycoon 2FA), the web pages used by Saiga feature the widely used ‘lorem ipsem’ pseudo-Latin placeholder text in the metadata fields.
This text is semantically meaningless and does not indicate the page’s purpose or function, helping attackers to avoid triggering keyword-based detection systems and brand impersonation heuristics.
Examples seen by Barracuda include:
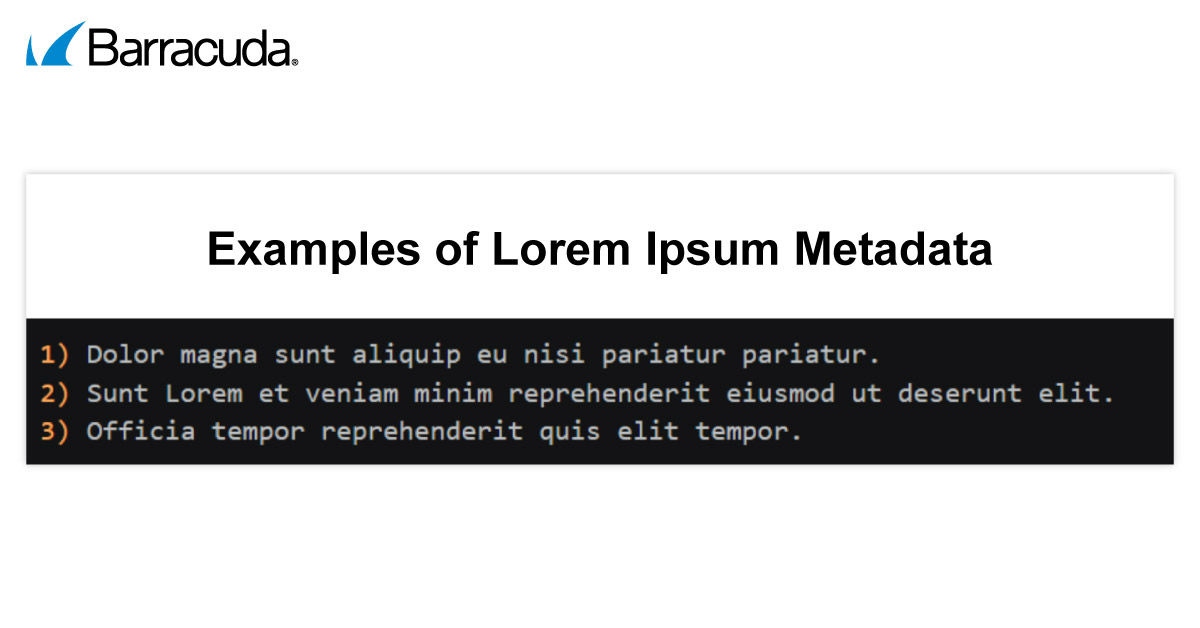
Saiga 2FA Phishing Kit - Examples of Lorem Ipsum Metadata
2. CAPTCHA gating
A custom Cloudflare Turnstile CAPTCHA is used to block bots, sandbox environments and automated security scanners, ensuring that only real human victims continue to the next stage.
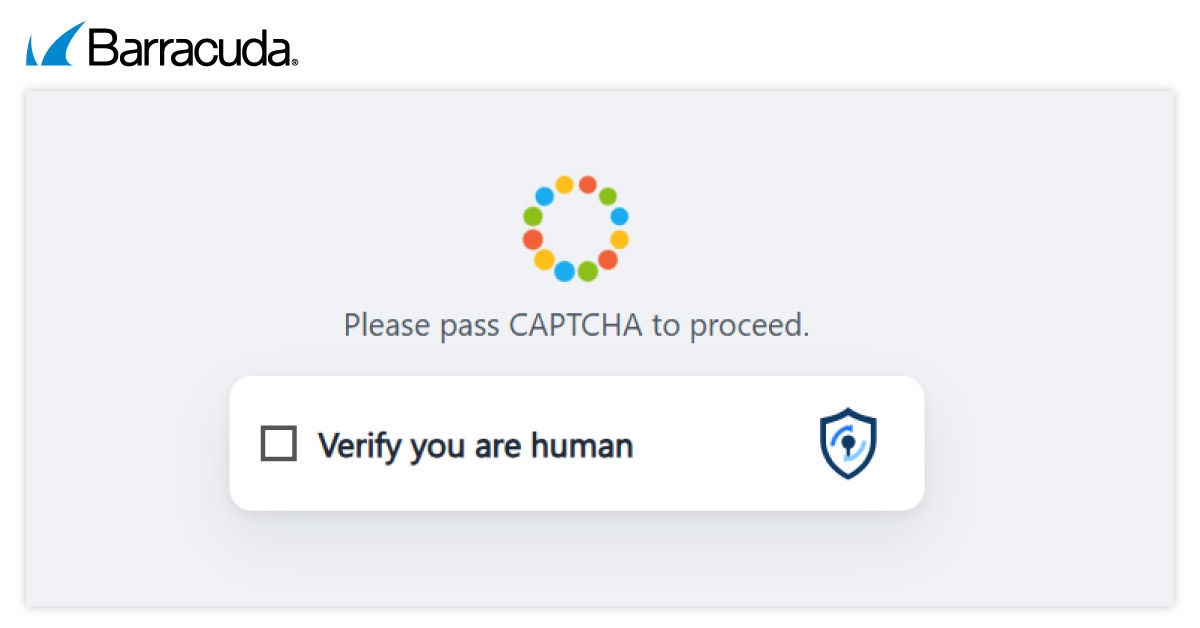
Saiga 2FA Phishing Kit - CAPTCHA Gating
3. Detection of developer tools
The Saiga 2FA framework detects when browser developer tools are opened and immediately redirects the user to a benign page such as Google search. This prevents security teams from inspecting and analyzing the pages.
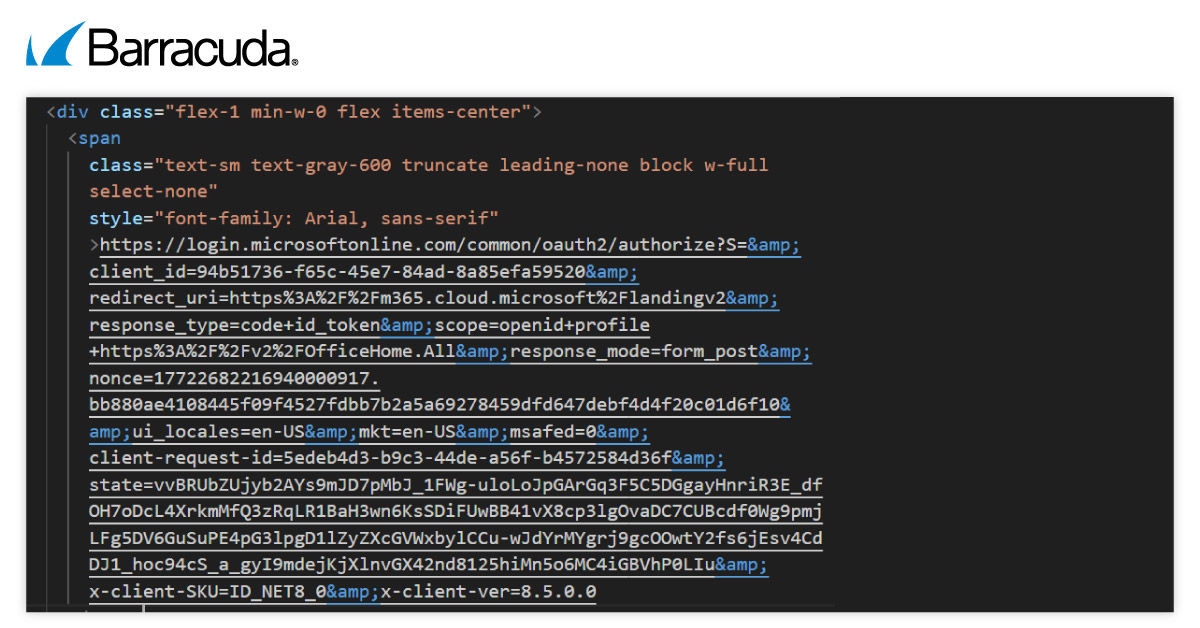
4. Dynamic page delivery using Next.js
Rather than using simple, fixed web pages, Saiga delivers its phishing pages as a full web application built with Next.js. The phishing content is generated on the fly using JavaScript, which makes it much harder for basic security scanners to spot anything malicious by simply inspecting the page source.
5. Selective content delivery and traffic filtering
Saiga uses built-in configuration settings, such as IP-based filtering, to decide who is shown the real phishing content. Based on factors like location or browsing environment, the framework can hide its malicious pages from security researchers and automated analysis tools, while still showing them to intended victims.
6. URL structure analysis
Initial URL:
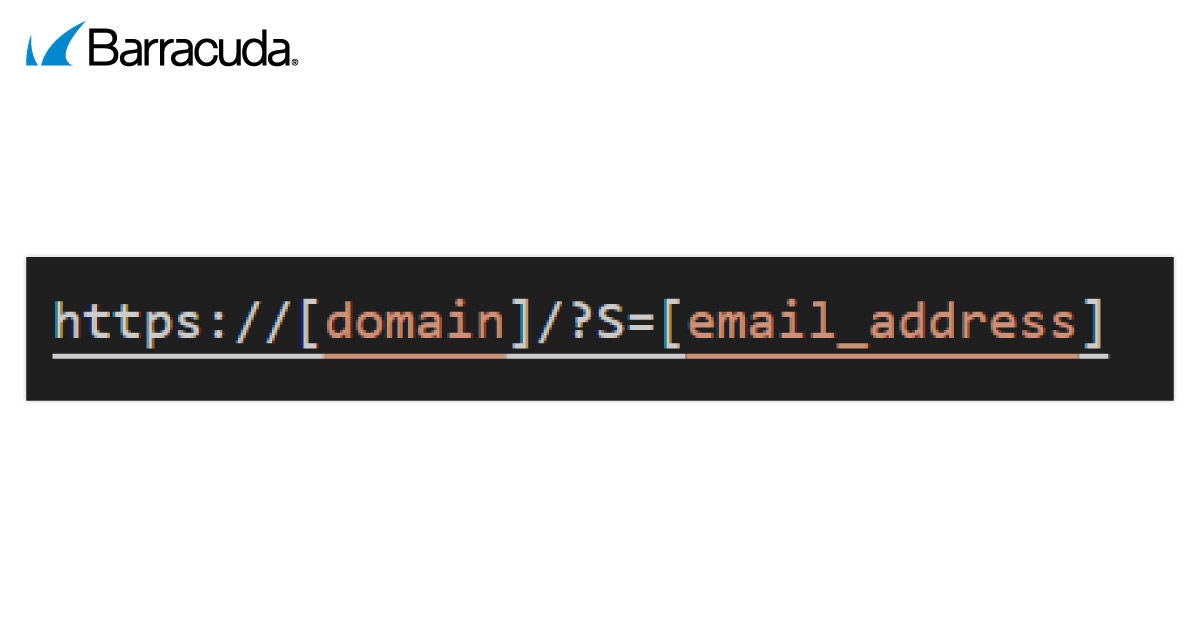
Saiga 2FA Phishing Kit - Initial URL structure
Redirected URL:
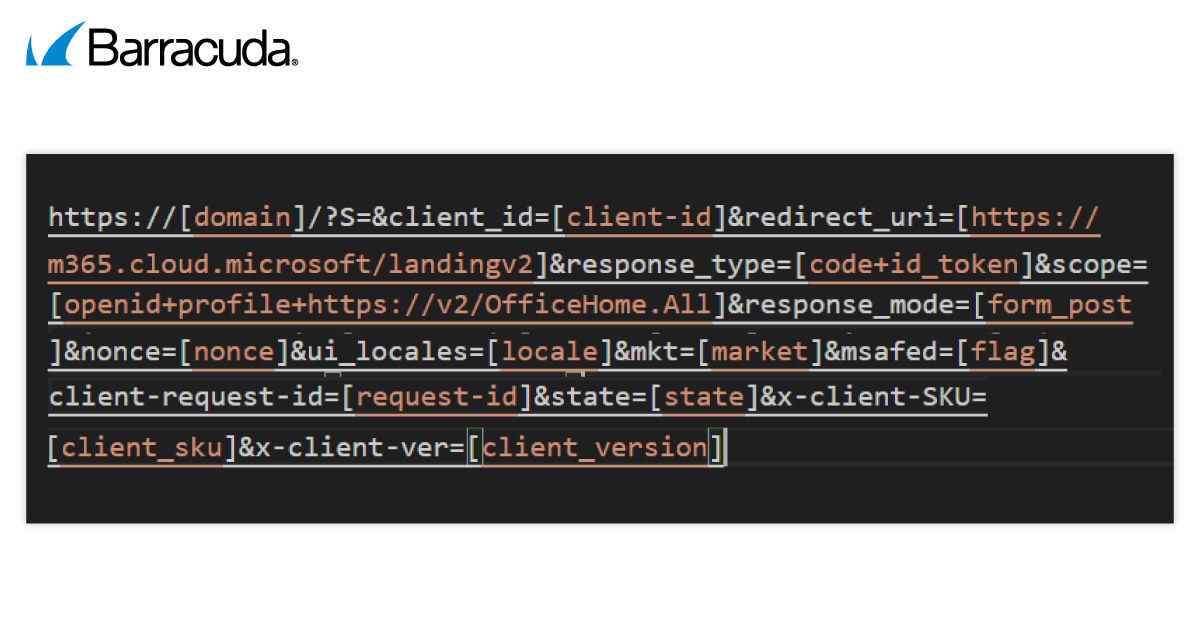
Saiga 2FA Phishing Kit - Redirected URL structure
Key observations from URL analysis:
- client_id, scope, response_type → mimic Microsoft OAuth flow
- redirect_uri → attacker-controlled but looks legitimate
- state, nonce → included for realism and session tracking
- S parameter → used for encoded victim targeting
- Additional parameters (client-request-id, x-client-*) → enhance authenticity
The application embeds a Microsoft OAuth authorization URL within the interface, mimicking a legitimate authentication request. However, this is purely visual and used to enhance credibility, as the authentication flow is fully controlled by the phishing infrastructure.
Saiga 2FA Phishing Kit - URL analysis
Frontend architecture and runtime behavior
Saiga 2FA Phishing Kit - frontend architecture and runtime behavior
The phishing page is not a simple, fixed HTML webpage. Instead, it is delivered as a fully built web application using Next.js, with key logic loaded dynamically when the page runs.
A configuration file embedded within the Next.js runtime controls how each phishing session behaves, including:
- Traffic filtering – deciding which visitors are shown the real phishing content
- CAPTCHA enforcement – requiring human verification before users can continue
- Notification controls – enabling or disabling alerts and prompts
- Redirect behavior – determining where users are sent at different stages
- Theme selection – changing the visual branding (for example, mimicking Microsoft 365)
- Feature toggles – enabling or disabling specific techniques such as browser‑in‑the‑browser (BIB)
Post-CAPTCHA flow
After CAPTCHA validation, the victim is shown a fake Adobe consent screen integrated with Microsoft login.
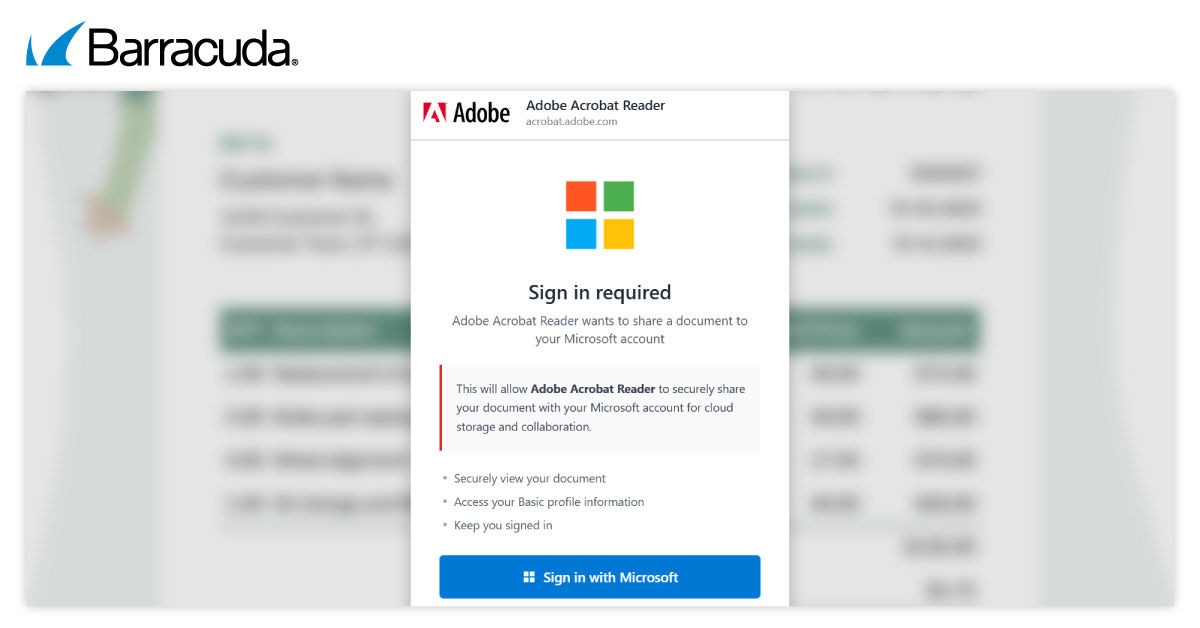
Saiga 2FA - Post-CAPTCHA flow
The victim is then redirected to a replica Microsoft login page where credentials are captured.
Saiga 2FA - Post-CAPTCHA flow
What sets Saiga 2FA apart from other phishing kits
While Saiga 2FA shares some of the core AiTM features with other phishing kits such as Sneaky 2FA and EvilProxy, there are a few differences:
- Saiga is not limited to credential harvesting. An integrated FM Scanner, a tool for extracting and analyzing mailbox content, enables attackers to search for and extract compromised mailbox data. This is reused via Saiga Mailer for further phishing campaigns.
- Saiga has a supported, small-scale operational strategy, targeting high-value victims with a focus on stealth, bypassing endpoint detection and response (EDR) solutions and controlled execution.
- Saiga’s infrastructure is based on a centralized platform known as Saiga-Hub. This provides a web-based dashboard for campaign lifecycle management, enables domain configuration, logging and automation, and implements advanced traffic filtering and conditional content loading. This level of centralization and control differentiates it from simpler phishing kits relying on Telegram-based logging.
- Saiga 2FA is typically more expensive than other PhaaS platforms, reflecting its advanced capabilities, integrated tooling and targeted operational model.
- Another key factor setting Saiga 2FA apart is its relatively low frequency in the wild. It has not been seen as often as some other high-volume phishing kits, and there is limited information available on the web. This scarcity adds to its effectiveness, as attackers can rely on its stealth to avoid detection for longer periods.
Conclusion
Saiga 2FA is an example of how phishing kits are evolving into application-level platforms. By combining dynamic frontend frameworks, runtime configuration and layered interaction flows, Saiga 2FA enables scalable and controlled phishing operations.
Unlike traditional phishing kits, Saiga integrates infrastructure, automation and post-compromise capabilities into a unified system, supporting advanced and highly targeted campaigns.
To mitigate against such attacks, organizations are advised to adopt phishing-resistant authentication methods such as FIDO2/WebAuthn, enforce strict URL verification practices and implement advanced monitoring to detect anomalous authentication behavior. A layered security approach is essential in defending against modern AitM phishing frameworks.
The Managed XDR Global Threat Report
Key findings about the tactics attackers use to target organizations and the security weak spots they try to exploit
Subscribe to the Barracuda Blog.
Sign up to receive threat spotlights, industry commentary, and more.

The Email Security Breach Report 2025
Key findings about the experience and impact of email security breaches on organizations worldwide