NightSpire: Wannabe warlords in ransomware’s shadow realm
How the NightSpire ransomware group blends old tactics with modern double‑extortion operations
Takeaways
- Resilience matters more than prevention against threat actors using common IT tools and credential abuse.
- Operational pressure, not just encryption, is the real threat. With tight ransom deadlines and an active data leak site, NightSpire weaponizes time, uncertainty and reputational risk to force rapid victim compliance.
- NightSpire has shown signs of immaturity, creating both risk for victims and opportunities for defenders.
NightSpire is a financially motivated ransomware group that was first observed in February 2025 and has claimed 259 victims across dozens of countries as of May 1, 2026. The group has an interesting backstory that will take us beyond its emergence, into 2024 when the NightSpire operators appear to have been working with other developers and different tools. We’ll come back to that. For now, here’s your quick overview:
| Threat type | Private ransomware group that signaled a transition to a ransomware-as-a-service (RaaS) model in April 2026. |
| Unique trait | One of the fastest capability escalations observed in an emerging group, despite glaring security failures such as using Gmail for victim communications and a server name that was directly attributable to an operator handle. |
| Targets | Companies of all sizes across all sectors. NightSpire is opportunistic and attacks where it finds an opportunity. |
| Initial access | CVE-2024-55591 exploits, Remote Desktop Protocol (RDP) brute-force attacks, phishing campaigns. |
| Extortion method | Double extortion using data exfiltration and encryption. |
| Leak site | Dedicated leak site (DLS) with victim list and a page listing non-payers and offering free downloads of stolen data. |
NightSpire kill chain
NightSpire follows a structured, multi-phase attack lifecycle that relies heavily on known vulnerabilities and freely available tooling. The binary is a Go (Golang)-compiled executable with multi-stage reconnaissance, obfuscation, and sophisticated encryption capabilities.
Initial access
NightSpire's primary initial access vector is CVE-2024-55591, a critical authentication bypass vulnerability in Fortinet FortiOS and FortiProxy. By sending crafted requests, an unauthenticated attacker can gain super-admin privileges and obtain full control of the device. Fortinet disclosed the flaw in January 2025, but exploitation had been observed as early as November 2024.
The group has also been observed using brute force and credential stuffing attacks, phishing campaigns, multifactor authentication (MFA) fatigue attacks, and remote monitoring and management (RMM) platform abuse. They’ll also use other exploits where they find an opportunity.
Lateral movement and privilege escalation
NightSpire uses living-off-the-land binaries (LOLBins) and a handful of legitimate third-party tools delivered in the attack. LOLBins like Conhost, PowerShell and WMI are used to execute commands and avoid detection. Utilities like Advanced IP Scanner and Everything.exe are used to map the network and search for financial records, internal communications, customer databases, and anything else the group identifies as valuable.
Credential harvesting is performed with Mimikatz, which extracts passwords, hashes, and Kerberos tickets from LSASS memory to escalate to domain admin privileges. AnyDesk is used for persistent remote access and hands-on-keyboard (HOK) access.
Data exfiltration
NightSpire collects files from the network using either native Windows copy utilities or a custom script for PowerShell. The files are packaged into encrypted archives using 7-Zip, then transferred to an attacker-controlled infrastructure using WinSCP, MEGACmd (Mega cloud storage), or Rclone.
Encryption and ransomware deployment
NightSpire uses a hybrid encryption strategy optimized for speed. Large files of certain types (iso, vhdx, vmdk) are encrypted in 1MB chunks, while all other files undergo full-file encryption. Most encrypted files are renamed with the ‘.nspire’ extension, but the group treats Microsoft OneDrive files differently.
NightSpire encrypts files stored in Microsoft OneDrive without changing icons or file extensions. When users access their OneDrive data, all filenames and icons remain intact, but the underlying data is corrupted and files cannot be opened. There are no visual clues to indicate encryption activity. This is considered an advanced operational capability because it is meant to delay detection and give the attack more time. It also avoids disrupting sync activity to the OneDrive cloud.
Here’s one of the NightSpire ransom notes:
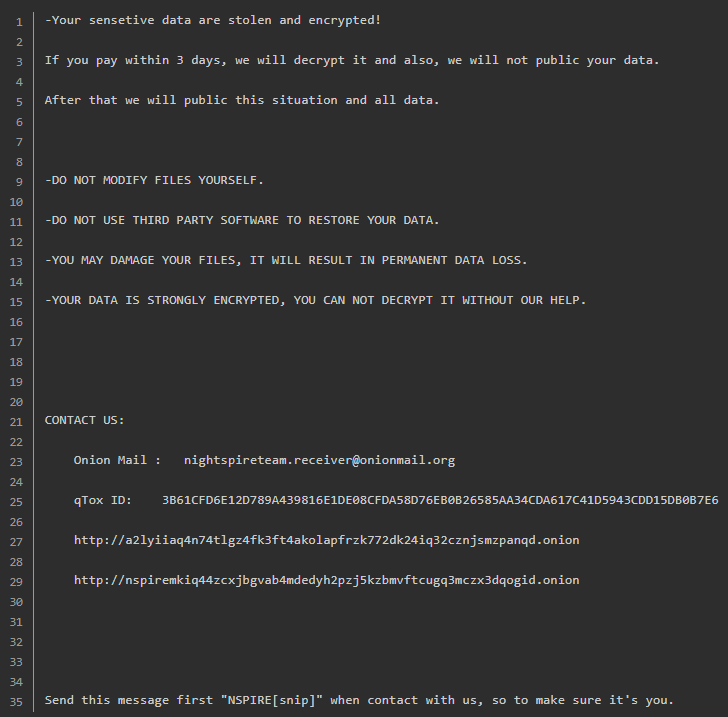
NightSpire ransom note, via Ransomware.live
Extortion and negotiation
NightSpire’s extortion strategy is aggressive and designed to create urgency and sustain pressure from multiple angles at once. Victims often have as little as 48 hours from the initial ransom note before stolen data is scheduled for publication. The group makes it hard for victims to avoid them by using multiple channels of communication in addition to its own negotiation portal. If negotiations stall, NightSpire may contact employees directly, leak portions of stolen data, or even publish excerpts of prior communications to increase reputational risk. If the victim does not pay, NightSpire releases the stolen data to other threat actors.
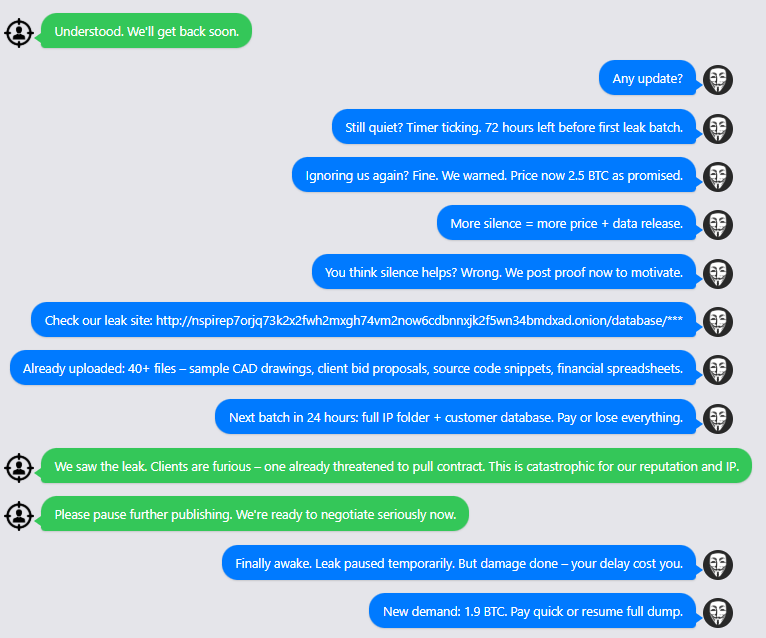
NightSpire negotiation chat, via Ransomware.live
Group name and logo
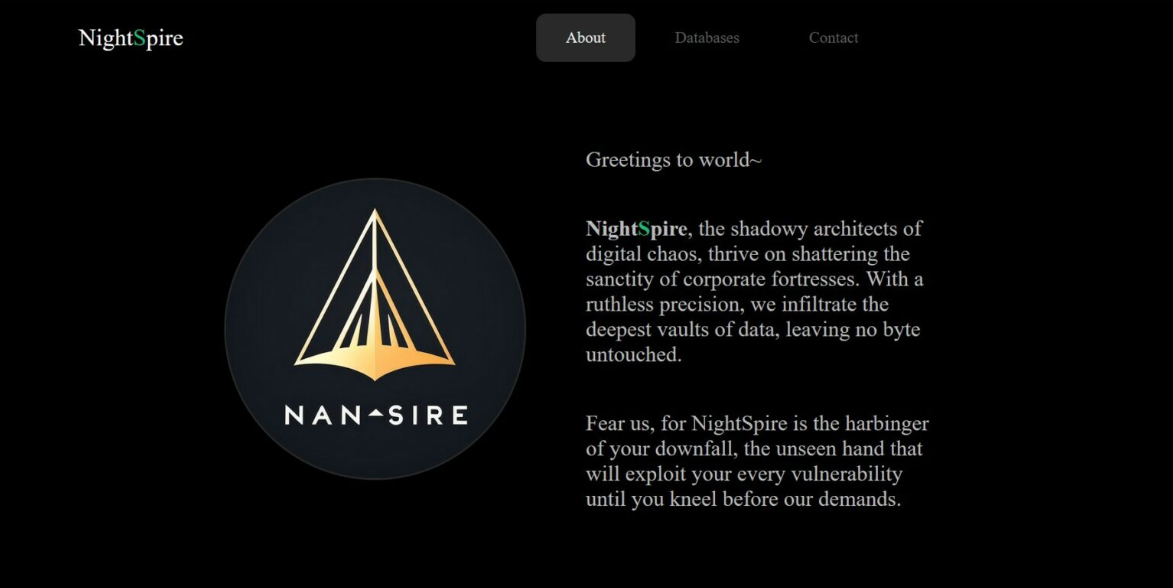
NightSpire DLS About page with logo and typical ransomware group messaging, via Red Hot Cyber
The NightSpire data leak site About page opens with "Greetings to world~" with a trailing tilde. The tilde is a documented marker of East Asian online communication, particularly Chinese internet culture. The text that follows is theatrical and grandiose and supports an assessment that the operators are younger operators attempting to build an intimidating identity.
NightSpire debuted their data leak site – and presumably their visual branding - in March 2025. Researchers quickly realized the potential hat tip to “Nightspire” in the World of Warcraft (WoW) universe, where Nightspire is both a seat of power and a high-level achievement. The group stylizes their brand name with a green capital S, which could symbolize the ‘fel green’ in WoW. It could also symbolize a dollar sign, or it could be both.
The logo features an angular spire or tower, rendered in gold tones against a black circle. The ‘NAN SIRE’ text beneath the graphic could mean anything, but ‘SIRE’ is a title for a lord or sovereign. The text on the page next to the logo includes “kneel before our demands.”
Keep in mind that these are interpretations of the NightSpire branding that the group has not publicly confirmed.
Location and identities
There isn’t much evidence to place NightSpire in any geographic location. No formal government attribution to any nation-state has been published, and no law enforcement actions, arrests, or indictments have been reported against NightSpire as of May 1, 2026. However, observed infrastructure and operator histories provide several geographic indicators that collectively point toward an India-linked operator nexus with possible Chinese-speaking involvement. The first of these was the tilde (~) we mentioned above.
The most concrete geographic indicator is IP address 14.139.185[.]60, first documented by S-RM in March 2025. This IP address was identified as the remote WinSCP data exfiltration server associated with NightSpire's infrastructure. The IP was republished as an Indicator of Compromise (IoC) by several other outlets and researchers, though no source specifies whether or when that IP was retired.
This IP address falls within a block assigned to Kerala Agricultural University on India's National Knowledge Network (NKN). This is a small, non-portable block of 16 IP addresses assigned to this university by India’s academic connectivity initiative. It’s possible the group was running its infrastructure out of the school, but many academic institutions have been compromised over the last several years. It seems more likely that NightSpire was taking advantage of a compromised host and a potentially high-bandwidth facility.
Two operator handles are known to be associated with NightSpire:
Xdragon128 (alias Xdragon333) is the primary public-facing operator. The handle follows classic gamer naming conventions — "dragon" plus a number — consistent with the broader gaming-culture aesthetic observed across the group's branding.
cuteliyuan is the second known operator. This handle contains "liyuan," a common Chinese given name, suggesting a Chinese-speaking individual. This aligns with the observations of East Asian cultural markers, like the tilde in the greeting on the NightSpire data leak site.
Origin story
NightSpire has documented connections to a chain of prior identities, tools and communities stretching back to mid-2024. What is interesting here is that this lineage runs through shared human operators rather than shared code.
Early operator sightings
In late 2024, actor ‘xdragon128’ was reported to be collaborating with ‘Paranodeus’ to build and promote the Python-based Parano toolset. This activity was observed in the DarkAssault and DeepWing Telegram groups. During this same period, xdragon128 appeared in hacktivist-adjacent channels linked to CyberVolk.
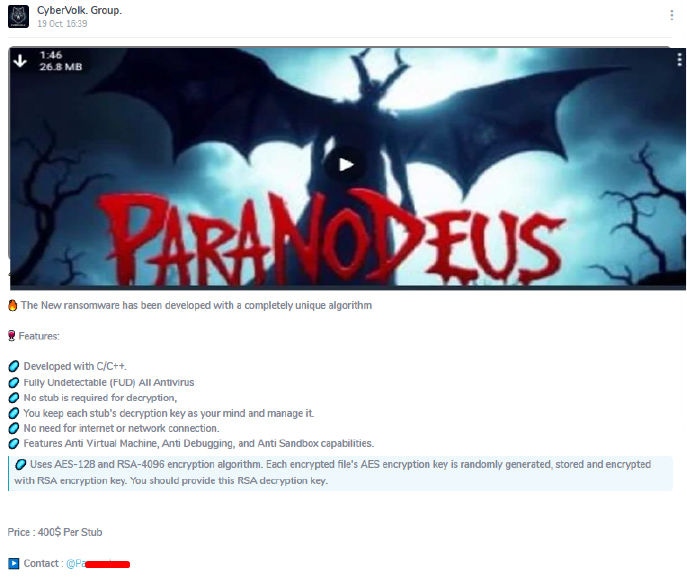
Paradoneus tools promoted by CyberVolk, via Cyfirma
This appears to be xdragon128’s early steps into the ransomware ecosystem.
There are multiple reports of Paranodeus and xdragon128 operating within the same Telegram communities and collaborating on Parano distribution. These Telegram channels were banned and there appear to be no available archives or screenshots. The forum images published here and here, taken together, seem to support the reported collaboration. There is additional research here that refers to “Paranodeus (aka xdragon128).” We do not have evidence to confirm the two handles represent the same individual.
Rbfs extortion operation
By early 2025, xdragon128 appears in the Rbfs extortion operation, which had a short lifespan and no clear branding. Here is a forum post announcing the status of a victim:
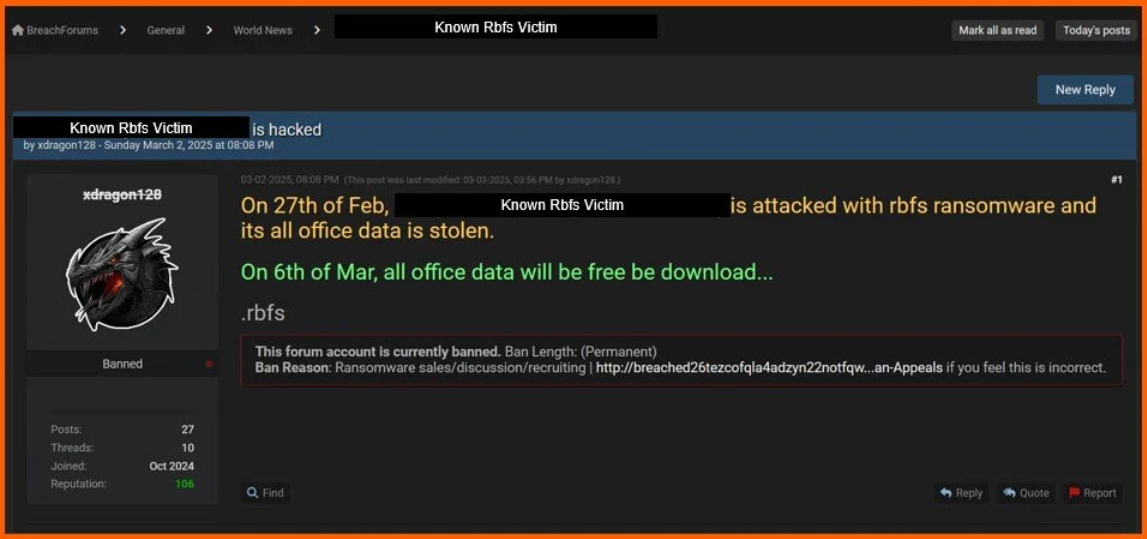
Xdragon128 post on Rbfs victim, via S-RM
Here is a partial screenshot of the NightSpire data leak site as of March 21, 2025, showing the same victim from the above image:

NightSpire victim list, via S-RM
You can see the full screenshots and additional shared victims here. Names were redacted by researchers.
At this point we have the first documented appearance of the second well-known NightSpire operator. Multiple sources report that the handle ‘cuteliyuan’ shared Telegram links to Rbfs victim data, suggesting coordinated activity immediately prior to NightSpire emergence. No screenshots or archived evidence of this activity appear to be publicly available, but the consistency across independent reporting provides supporting context.
Rebranding to NightSpire
The transition from Rbfs to NightSpire occurs abruptly in early March 2025, with Rbfs activity ceasing as NightSpire emerges within the same timeframe. Multiple sources identify shared operators and overlapping victims, as described above. Indicators of infrastructure continuity further support this link, including the hostname “XDRAGON-SERVER1,” which has been attributed to the xdragon128 persona in early incident reporting.
NightSpire shares clear lineage with the earlier Rbfs operation, but there are several notable differences in both capability and execution.
- The Go-based ransomware payload represents a shift away from earlier Python-based tooling associated with the Parano ecosystem. This suggests a break in underlying malware development.
- NightSpire operates a full double-extortion model, combining encryption with a dedicated leak site and structured victim publication. Rbfs was only observed using data-only extortion.
- The early months of NightSpire were marked by elements of operational immaturity. Researchers found exposed directory listings and identifiable infrastructure. Negotiations were sometimes conducted through Gmail, which introduced the risk of account disruption during active negotiations.
The continuity of core operators, combined with the abrupt transition timeline and indicators of infrastructure continuity, supports the assessment that NightSpire represents a reorganization and scaling effort rather than a fresh start. Earlier activity places Paranodeus within the same ecosystem, but there is no direct evidence linking that identity or the Parano toolset to NightSpire operations.
Indications of a ransomware-as-a-service (RaaS) model
Reports published in April 2026 show screenshots of NightSpire inviting affiliates to contact them.
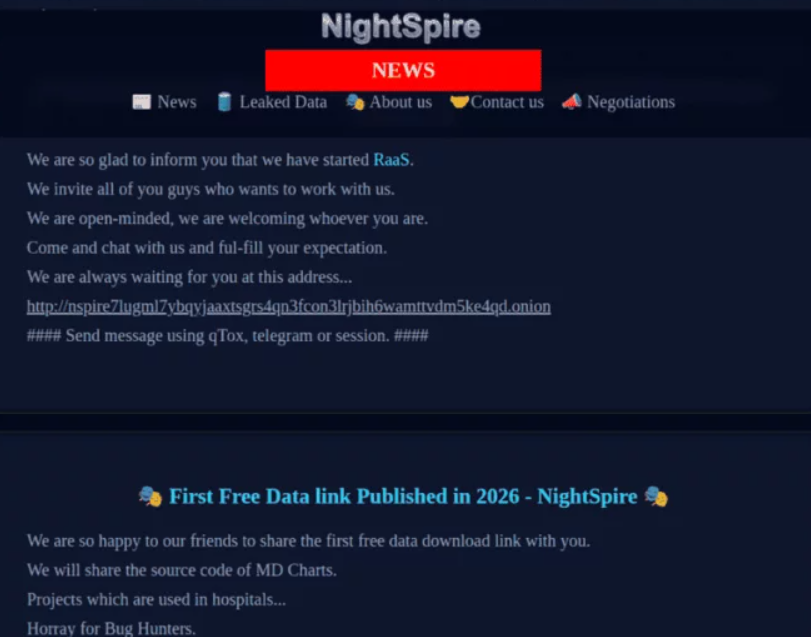
RaaS announcement on NightSpire data leak site, via SOSRansomware
This would mark NightSpire’s first public move toward affiliate-based scaling.
NightSpire represents a rapid maturation into a full double-extortion ransomware group, introducing a Go-based payload and scaling victim operations while maintaining continuity of the same core actors. The progression highlights a deliberate transition from community-driven tooling and experimentation to a structured, revenue-focused ransomware operation—driven by shared personnel, not shared code.
What this means for you
NightSpire’s rapid progression highlights how quickly ransomware operations are evolving.
Business leaders must prioritize resilience. This includes ensuring that critical data is protected and recoverable, understanding how quickly systems can be restored, and preparing for the possibility of data exposure—not just encryption. The impact of a ransomware incident now extends beyond downtime to include regulatory risk, reputational damage, and loss of customer trust.
Security investments should be evaluated based on how well they reduce the impact of an attack, not just how well they prevent one. This includes having an incident response plan that accounts for both ransomware and data breach scenarios, with defined roles across legal, communications, and operations.
The goal is not to outthink attackers at every step, but to ensure that your organization can detect, respond, and recover quickly while you stay focused on running the business. You can augment your efforts with a managed service provider (MSP) or another third-party provider to help with this.
For MSPs and IT teams, the NightSpire timeline highlights the importance of speed—specifically, how quickly an attacker can move from initial access to full compromise. Once inside, attackers increasingly rely on legitimate tools and quiet techniques to identify, collect and stage data before deploying ransomware. This makes early detection and containment critical.
Defenders should prioritize visibility into user activity, file access patterns, and data movement, particularly in cloud environments such as Microsoft 365. Strong identity controls—including multi-factor authentication and conditional access—are essential to reduce the risk of account takeover, which remains a common entry point. In addition, organizations should ensure that backups are not only available but immutable, regularly tested, and capable of rapid restoration.
For MSPs, this risk is amplified across multiple customers. A single compromise can cascade across environments if controls are not properly segmented. As ransomware groups show early signs of scaling toward ransomware-as-a-service models, MSPs should assume that attacks will become more frequent and more distributed. Proactive monitoring, standardized security controls, and rapid response capabilities are key to reducing both the likelihood and impact of these attacks.
Barracuda can help
Maximize your protection and cyber resilience with the BarracudaONE AI-powered cybersecurity platform. The platform protects your email, data, applications, and networks, and is strengthened by a 24/7 managed XDR service, unifying your security defenses and providing deep, intelligent threat detection and response. Manage your organization’s security posture with confidence, leveraging advanced protection, real-time analytics and proactive response capabilities. Robust reporting tools provide clear, actionable insights, helping you monitor risks, measure ROI and demonstrate operational impact. Don’t miss the opportunity to get a demo of the platform from our cybersecurity experts.

2026 Email Threats Report
Learn how AI and phishing-as-a-service are reshaping the email threat landscape and how to stay protected
Subscribe to the Barracuda Blog.
Sign up to receive threat spotlights, industry commentary, and more.
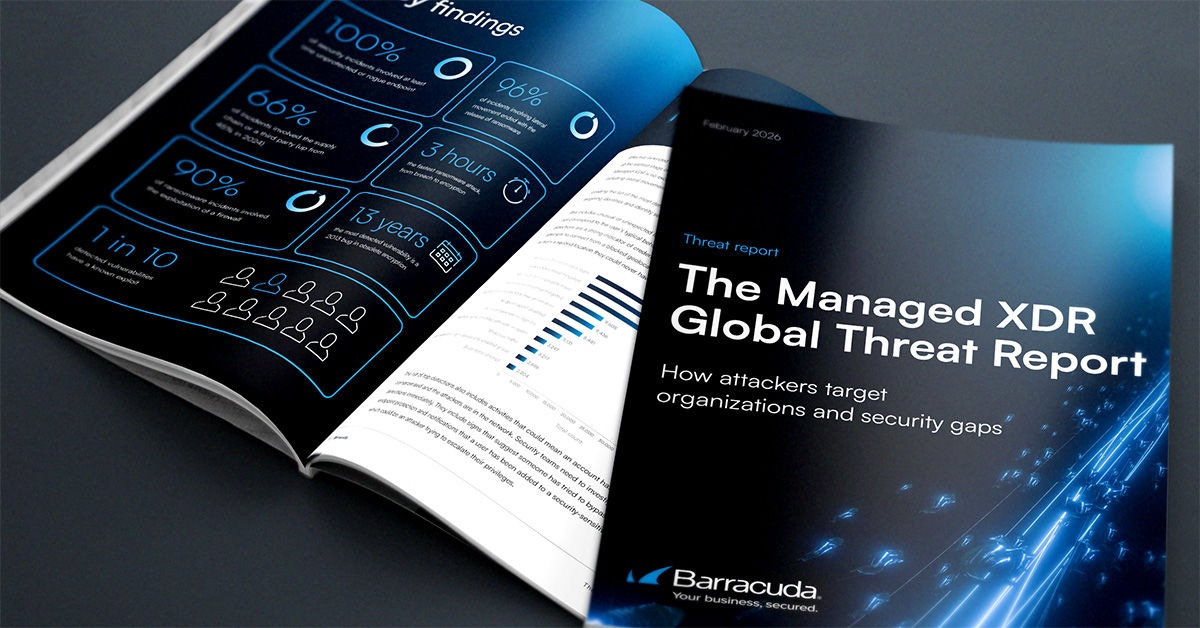
The Managed XDR Global Threat Report
Key findings about the tactics attackers use to target organizations and the security weak spots they try to exploit