The ‘code of conduct’ phishing campaign: What MSPs need to know right now
How an AiTM phishing campaign used clean infrastructure and compliance lures to bypass MFA at scale
Takeaways
- The “code of conduct” phishing campaign avoids botnets, compromised servers, and other signals used by security tools
- Adversary‑in‑the‑middle (AiTM) phishing turns valid user actions into the attack vector
- Resilience now depends on limiting blast radius, not perfect prevention
Microsoft researchers observed a sophisticated, multi-stage phishing campaign that affected more than 35,000 users across 13,000 organizations. The attacks hit companies in 26 countries, though most (92%) were in the United States. Several industries including healthcare and financial services were targeted. The campaign uses a ‘code of conduct’ violation as a phishing lure, which is the basis for the name.
Why is this significant?
This phishing campaign was a multi-stage operation that included:
- Fake/impersonated internal HR and compliance communications
- Adversary-in-the-middle (AiTM) techniques to defeat multifactor authentication (MFA) in real time
- Multiple CAPTCHA gates and staging pages designed to evade automated security analysis.
None of these techniques are new. The significance is how cleanly they have been combined and deployed at scale.
No botnet required
One of the most important things to understand about this campaign is that it does not rely on compromised devices or a traditional botnet to distribute its payload. The entire AiTM phishing kit is deployed through common commercial services:
- Phishing kit: The operators lease access to an AiTM phishing-as-a-service (PhaaS) kit, like the recently disrupted Tycoon 2FA. These kits include the pre-built credential harvesting pages, CAPTCHA gating, session token interception, and real-time victim monitoring dashboards. Pricing starts as low as $120 for 10 days of access.
- Cloud-hosted virtual machines: Rather than using compromised machines, the campaign infrastructure was likely hosted on commercial cloud VMs available to the public.
- Commercial email delivery services: The campaign emails were sent through a standard email delivery platform, passing the SPF, DKIM, and DMARC checks that would normally flag suspicious mail. These messages didn’t look like phishing attacks because they were properly formatted and sent from domains the attackers had registered and configured correctly.
- Attacker-controlled domains mimicking trusted brands: Researchers observed landing pages behind domains like `acceptable-use-policy-calendly[.]de` and `compliance-protectionoutlook[.]de. `These domains are designed to look like widely-known brand services at-a-glance.
How the attack works
This campaign follows a well-established AiTM phishing model, combining commercially available phishing kits, legitimate cloud infrastructure and psychologically effective lures to steal credentials and session tokens in real time.
Tool acquisition and infrastructure build: The attacker purchases access to a PhaaS kit that provides pre-built credential harvesting pages, CAPTCHA gating, and AiTM session interception. The kit may offer domains, or the attacker purchases the phishing domains separately. An email delivery service is configured on a rented Windows VM. This is used to send authenticated messages from the phishing domains. This part of the attack takes a few hours and costs just a few hundred dollars.
Delivery: The attacker sends phishing emails to targets using display names like "Internal Regulatory COC" and "Workforce Communications," with subject lines such as "Internal case log issued under conduct policy" and "Reminder: employer opened a non-compliance case log."
The lure: Each email includes a PDF attachment with a filename like "Awareness Case Log File – Tuesday 14th, April 2026.pdf" or "Disciplinary Action – Employee Device Handling Case.pdf." The PDF provides a fictional summary of a conduct review process and instructs the recipient to click a "Review Case Materials" link to access supporting documentation.
This ‘Review Case Materials’ link is the entry point to the credential harvesting flow.
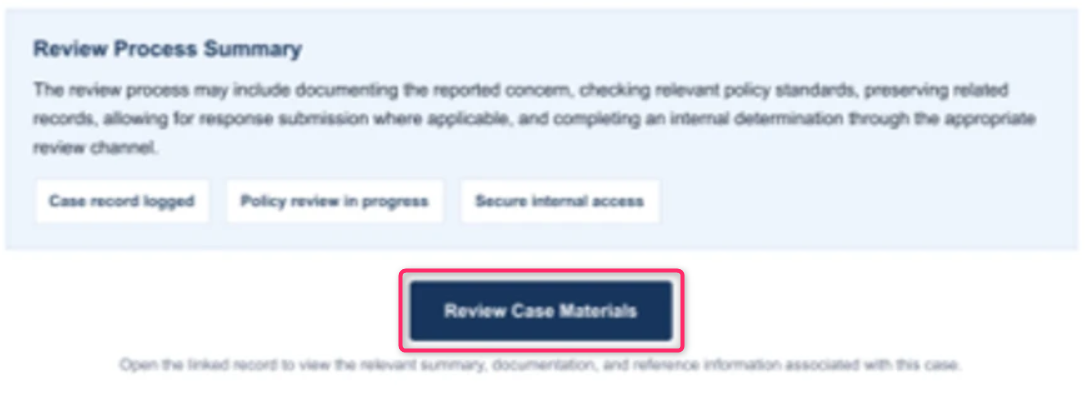
Partial image of pdf document from the ‘code of conduct’ campaign, via Microsoft.
First CAPTCHA gate: Clicking the ‘Review Case Materials’ link redirects the user to an attacker-controlled landing page that displays a Cloudflare CAPTCHA. The CAPTCHA is presented as validating that the user is coming "from a valid session," but it has two malicious purposes:
- It reinforces the appearance of a genuine security process
- It blocks automated security tools and sandbox environments from analyzing what comes next.
The setup: After completing the CAPTCHA, the user is redirected to an intermediate staging page that tells them the requested documentation is encrypted and requires account authentication to access. The page presents a "Review & Sign" button and prompts the user to enter their email address.
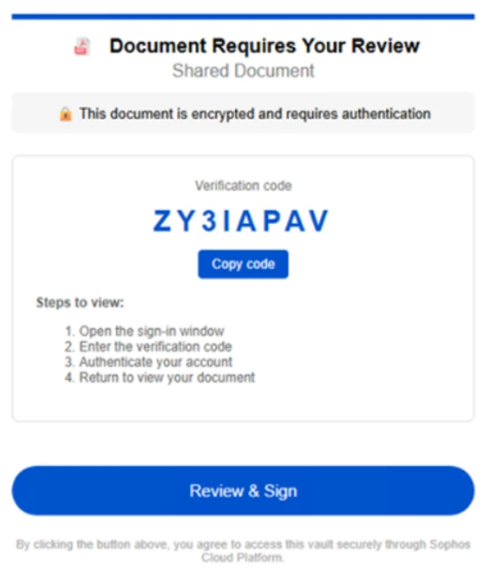
Phishing page asking users to click ‘Review & Sign,’ via Microsoft
Second CAPTCHA gate: After submitting their email address, the user is presented with a second CAPTCHA — this time an image selection challenge. This additional gate is a second filter to evade automated analysis.
Common image selection CAPTCHA challenge
The confidence build: Once the second CAPTCHA is completed, the user sees a confirmation message stating that verification was successful and that their "case" materials are being prepared. They are then told to sign in with their Microsoft account within five minutes or the link will expire. The countdown creates urgency and discourages the user from pausing to question the process.
Credential and token capture: The user clicks a "Sign in with Microsoft" button that initiates the AiTM session, which allows the attacker to position their server between the victim and the Microsoft server. Now the user is only seeing the pages that are controlled by the attacker. If the user enters their credentials and completes the MFA challenge as normal, the attacker will intercept the session token as it's issued. The attacker now has authenticated access to the victim's account and authorized services.
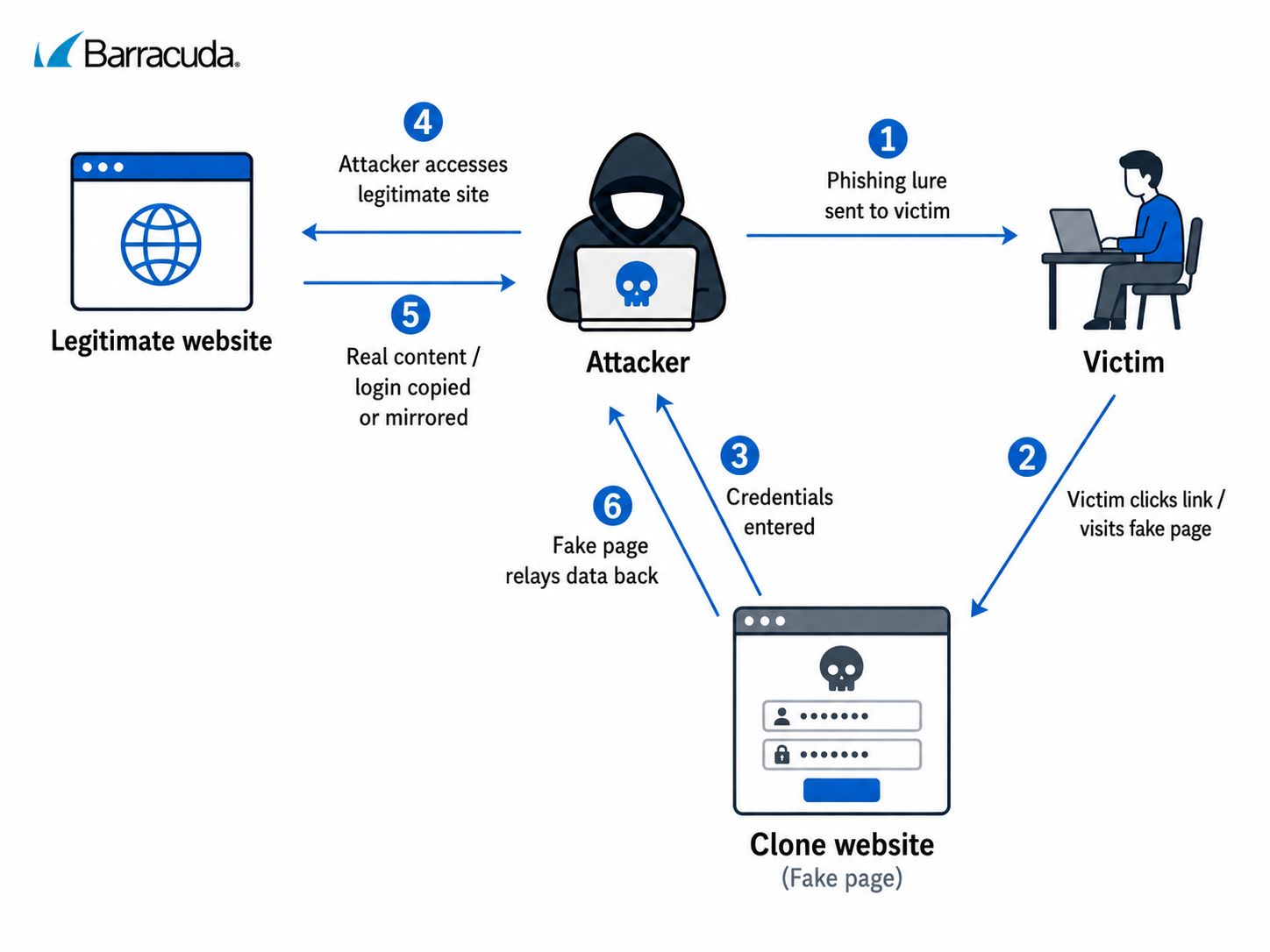
Credential-harvesting phishing workflow. AI-generated illustration for educational purposes
This campaign is a precision operation built on commercial services and commodity criminal tools, and it can be accessed with a few hundred dollars and a Telegram account. The infrastructure is disposable, replaceable, and difficult to distinguish from normal business email traffic at the network level.
Why this is high-risk phishing
This campaign is more dangerous than traditional botnet‑driven phishing because it relies almost entirely on properly configured commercial infrastructure and avoids many of the technical signals that security controls are designed to detect. For example:
Infrastructure
- Use of standard enterprise email delivery services rather than compromised hosts
- Properly authenticated domains with valid SPF, DKIM, and DMARC alignment
- Cloud-hosted phishing infrastructure with no prior abuse reputation
- No reliance on known botnet IP ranges or previously abused networks
Delivery
- Low‑volume, targeted delivery that avoids burst or spray‑and‑pray patterns
- Clean SMTP headers and standard mail routing paths
- No rapid IP or domain churn commonly associated with botnet operations
Content and interaction
- Contextual lures tied to corporate policy and compliance workflows
- Multi‑step redirect chains designed to frustrate automated analysis
- Adversary‑in‑the‑middle proxies that operate inline with genuine Microsoft authentication flows rather than static credential capture pages
These characteristics contrast sharply with botnet‑driven phishing campaigns. Helpful signals like reputation-based indicators, malformed delivery paths and reused phishing templates are largely absent here.
Specific takeaways for MSPs
Managed service providers operate at the intersection of identity, access and scale. A single successful AiTM phishing event can potentially provide attackers with access to multiple customer environments through delegated administration, shared tooling or elevated service accounts. The following steps highlight ways MSPs can better protect themselves and their clients from attacks where traditional controls and assumptions may fall short.
Audit your clients' MFA implementations. SMS codes, authenticator app one-time passwords (OTPs), and push-based MFA are all vulnerable to AiTM session hijacking. Conditional access policies that evaluate device compliance, IP location, and sign-in risk can reduce exposure in the near term, but the definitive fix is phishing-resistant authentication. Begin planning migrations to FIDO2 security keys or passkey-based authentication for privileged accounts first, then expand to the broader user base.
Treat PhaaS fragmentation events as an acceleration of risk, not a reduction. The Tycoon 2FA takedown didn't shrink the threat — it distributed it. Multiple kits with overlapping capabilities are now competing for operator market share. That means more operators, more campaigns, more technique variation, and less predictable infrastructure. Signature-based detection will fall further behind.
Review email security stacks for AiTM-specific detection gaps. Can your email security solution detect when a legitimate email delivery service is being used to send phishing from properly authenticated attacker-controlled domains? Can it inspect PDFs for embedded links? Can it evaluate post-click redirect chains through CAPTCHA gates? If the answer to any of these is no, you have a gap this campaign would exploit.
Prepare clients for the “code of conduct” lure. Ensure they train employees to verify unexpected HR or compliance messages through a separate channel before clicking anything.
Monitor for post-compromise signals aggressively. Don't wait for a phishing email to be caught. Monitor for anomalous sign-in properties, impossible travel and other unusual activity. AiTM attacks are fast-moving — the window between session hijack and attack damage can be measured in minutes, not hours.
Communicate with clients about the MFA gap. Many clients still believe MFA makes them safe from phishing. This campaign is a concrete, well-documented example that proves otherwise. Use it to start the conversation about phishing-resistant authentication, conditional access and layered identity protection.
For MSPs, campaigns like Code of Conduct highlight a shift from prevention-first thinking to resilience-first outcomes. When phishing activity blends into common infrastructure and authentication flows, the question is no longer whether every attack can be stopped, but how much damage occurs when one gets through. Limiting blast radius through identity boundaries, constrained privileges, and rapid response becomes the defining measure of security effectiveness. Resilience depends on containing the impact of an attack before a single compromised user turns into a multi‑tenant incident.
The Managed XDR Global Threat Report
Key findings about the tactics attackers use to target organizations and the security weak spots they try to exploit
Subscribe to the Barracuda Blog.
Sign up to receive threat spotlights, industry commentary, and more.

The Email Security Breach Report 2025
Key findings about the experience and impact of email security breaches on organizations worldwide