Malware Brief: Air gaps breached, CPUs hijacked and supply‑chain chaos
Exploring how cyber attackers are undermining trust by targeting isolated systems, hijacking hardware and exploiting the software supply chain
Key takeaways
- Attackers are exploiting assumed trust in isolation models, business workflows and software supply chains.
- Malware distribution increasingly hides inside routine enterprise activity, including hiring and development pipelines.
- Automated and self‑propagating supply‑chain threats reduce defenders’ reaction time and increase blast radius.
This Malware Brief highlights three very different threats that share a common theme: attackers are going where controls are weakest and trust is highest.
APT37 Ruby Jumper: Breaching air‑gapped systems
Key facts
- Threat actor: APT37 (aka ScarCruft), linked to North Korea
- Malware/toolkit: Ruby Jumper
- Target: Air‑gapped and segmented environments
- Initial access: Malicious files plus removable media
- Notable tactic: Cloud services combined with USB propagation
Observers have spotted APT37 using Ruby Jumper, a toolkit designed to move commands and data between internet‑connected and air‑gapped systems. Rather than relying on unusual side‑channel exploits, Ruby Jumper uses vectors that have proven reliable in many forms of attack: people, removable media and legitimate cloud services.
Researchers report that the malware stages data on USB devices and leverages cloud storage platforms for command‑and‑control, allowing instructions to move across environments whenever trusted users do the same. Barracuda threat telemetry consistently shows that removable media and trusted workflows remain recurring weak points in otherwise well‑segmented environments.
This recent blog post discusses vulnerabilities in air-gapped systems more fully.
FAUX#ELEVATE: Fake résumés, real cryptomining
Key facts
- Malware family: FAUX#ELEVATE
- Payload: Illicit Monero cryptominer
- Primary impact: Stolen CPU cycles and degraded system performance
- Distribution method: Multiple, including weaponized résumé files sent to recruiters
FAUX#ELEVATE is a reminder that malware does not need to be sophisticated to be effective. The threat installs a covert Monero cryptominer, quietly consuming CPU resources while leaving victims with sluggish performance, overheating systems and higher power consumption.
Recent reporting shows the malware delivered through fake job applications, where malicious résumé files are sent directly to HR teams. Barracuda Research telemetry regularly shows malware attempting to blend into routine business processes. Hiring workflows remain especially attractive because opening attachments from unknown senders is part of the job.
Cryptomining malware like this often persists and goes undetected longer than more disruptive threats because it avoids obvious damage. The result is a slow, accumulating cost that many organizations don’t immediately connect back to malware activity.
CanisterWorm: Supply‑chain malware that spreads itself
Key facts
- Malware: CanisterWorm
- Attack type: Supply‑chain compromise
- Target: Open‑source packages and build pipelines
- Notable behavior: Self‑propagating infection across ecosystems
CanisterWorm highlights how supply‑chain attacks continue to evolve toward automation and speed. Rather than remaining isolated in a single project, the malware actively propagates through package registries and CI/CD environments as developers unknowingly pull in infected components.
Researchers describe behavior that resembles a worm optimized for modern software development workflows. Barracuda threat data increasingly reflects this shift: Once a compromised dependency enters the ecosystem, downstream exposure can expand rapidly before defenders have visibility.
The challenge is not just detection, but containment. The longer these infections circulate through interconnected build systems, the harder recovery becomes.
Why this matters
Across these three threats, the pattern is consistent:
- Physical isolation is treated as a control instead of a risk reduction.
- Routine workflows are trusted by default.
- Software dependencies are inherited without enough scrutiny.
Barracuda’s global threat data continues to show attackers taking advantage of each of these assumptions.
BarracudaONE, our cybersecurity platform, uses advanced machine learning and a groundbreaking set of integrated capabilities to deliver total visibility, detection and response across your infrastructure, protecting your entire attack surface even as it grows more complex.
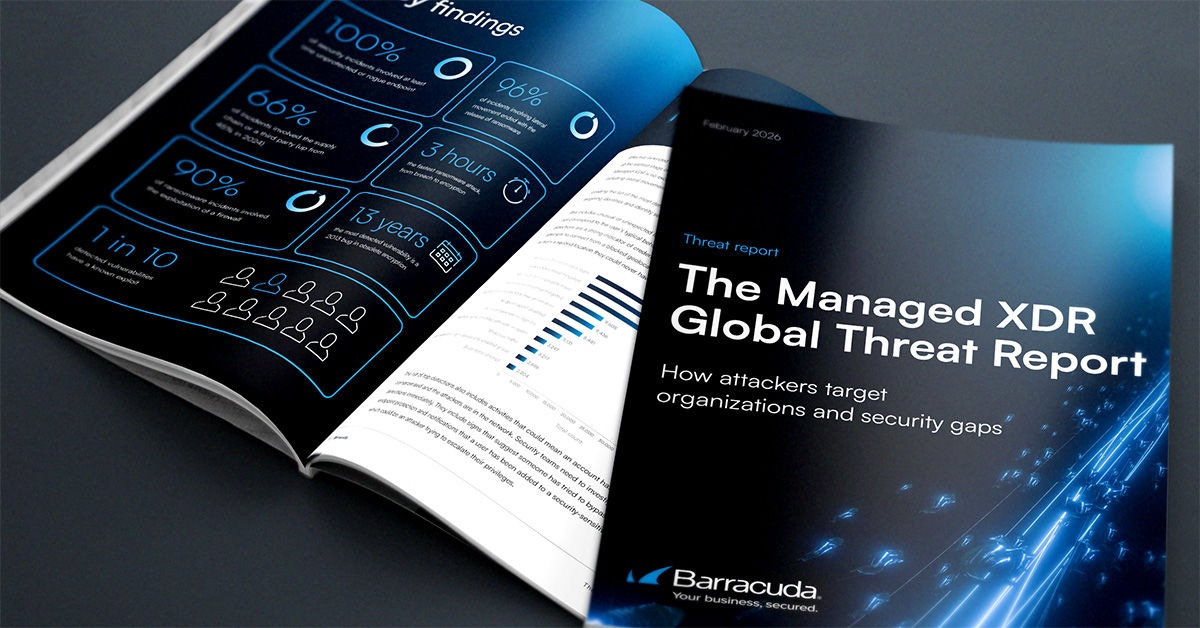
The Managed XDR Global Threat Report
Key findings about the tactics attackers use to target organizations and the security weak spots they try to exploit
Subscribe to the Barracuda Blog.
Sign up to receive threat spotlights, industry commentary, and more.

The Email Security Breach Report 2025
Key findings about the experience and impact of email security breaches on organizations worldwide