The gig economy of cybercrime
You’ve probably heard the term ‘gig economy,’ which refers to a labor market characterized by short-term jobs, or gigs. These gigs are project-based and arranged through digital platforms or informal networks. Workers take on assignments as needed, much like a designer might pick up a job through Fiverrr or Freelancer. A gig economy is built on agility, specialization and on-demand collaboration, and it’s working really well for the threat actors running ransomware and other criminal operations.
Background
One thing that most threat actors have in common is that they aren’t stuck on a single brand. Sure, we’ll always have those outliers like LockBit and state-employed espionage actors, but most cybercriminals have no brand identity or loyalty to branded groups.
You could see the writing on the wall when Ransomware-as-a-Service (RaaS) became a thing. Affiliates were free to come and go, depending on the rules of the RaaS. Some RaaS groups do everything from providing phishing platforms for initial access to negotiating and collecting the ransoms. The affiliate just has to conduct a successful attack. If the attacker is named in the media, it’s always a brand like Akira, Medusa, Fog, Rhysida. Occasionally you’ll see the name of an affiliate if the affiliate is also a brand.
Prior to the RaaS model, there were exploit kits like Angler and some Spam-as-a-Service platforms that enabled threat actors to rent tools and infrastructure. These models were the first pieces of the massive cybercrime supply chain we see today. RaaS was the first model to fully separate identity, operations and branding. This accelerated the evolution of decentralized cybercrime operations.
The European Union Agency for Cybersecurity (ENISA) examined the growth of this modular, service-based structure in its 2022 ENISA Threat Landscape. This report highlights “the increased diversification, professionalisation and specialisation of threat groups” and the "mix and match" nature of different affiliates involved in different phases of the intrusion. There are many other findings in the report that show how the criminal economy is adopting gig economy principles.
Modular talent and project-based crime
Let’s look at the specialized roles you might find in a ransomware attack chain:
- Initial access: Initial Access Brokers (IABs), phishing and social engineering specialists, callers / talkers, exploit developers
- Discovery, lateral movement, enumeration: Reconnaissance specialists/intrusion operators, malware loaders/payload deployment specialists, script developers
- Persistence, privilege escalation: Penetration experts/post-exploitation operators
- Defense evasion: Security evasion experts and obfuscation engineers
- Data exfiltration: Data thieves, exfiltration experts
- Ransomware deployment: Ransomware developers, infrastructure operators
- Extortion & negotiation: Ransom note authors, negotiators/communication specialists, PR/leak site managers
SafePay and HelloGookie make use of callers and talkers, Qilin has a lawyer on call, and Anubis connects data thieves with experts in monetizing stolen data. DragonForce specifically offers project collaboration to other groups. Not all these roles are performed by separate individuals, but all these groups have different specialties and niche talents at work.
Collectives and cartels
Another characteristic of the modern cybercrime economy is that threat actors may operate as a loose collective that shares resources. There are some high-profile examples of this, including the DragonForce Ransomware Cartel (DFRC), which is a decentralized coalition of threat actors. Cartel members can launch attacks under their own brands while using DragonForce resources, which include malware, attack management tools, storage, and ‘a reliable infrastructure.’ Threat actors can use these resources to collaborate and share with each other as desired, and the DragonForce core operators take the agreed-upon cut for their services. As a cartel, DFRC also conducts press relations and will use publicity to pressure victims and pursue dominance in the threat landscape.
Scattered Spider is another example of a decentralized group of actors that specialize in social engineering, SIM swapping and identity impersonation—techniques often associated with advanced persistent threats (APTs). Lapsus$ is a similar group specializing in social engineering and exploiting multi-factor authentication (MFA) to gain access to networks.
Both groups emerged from a larger, loose-knit collective known as ‘The Com,’ which is short for ‘The Community.’ Associates of The Com usually come up through online gaming and other internet spaces. Darknet Diaries interviewed a member of The Com in 2022. You can listen to the podcast or read the transcript here.
What This Means for Defenders
This gig model makes the cybercrime economy more resilient. If a threat actor isn’t arrested, he just moves to another space. IT teams have to think about how to defend against the gig threat model. Security has to be broad, behavior-based, and layered:
- Use behavioral detection and threat hunting, not just known indicators of compromise.
- Monitor for unusual access patterns and privilege escalation.
- Train employees to recognize vishing, phishing, and impersonation tactics.
- Apply zero trust principles—assume compromise, verify every access attempt.
- Stay informed through threat intelligence on emerging underground tools and services.
Barracuda can help
With an AI-powered cybersecurity platform, your business can maximize protection and cyber resilience. A unified platform that provides advanced protection, real-time analytics and proactive response capabilities helps eliminate security gaps, reduce operational complexity and improve visibility. By consolidating key security functions, a cybersecurity platform can minimize your administrative burden and simplify operations. With guidance from cybersecurity experts, you can leverage all the benefits of a unified cybersecurity platform.
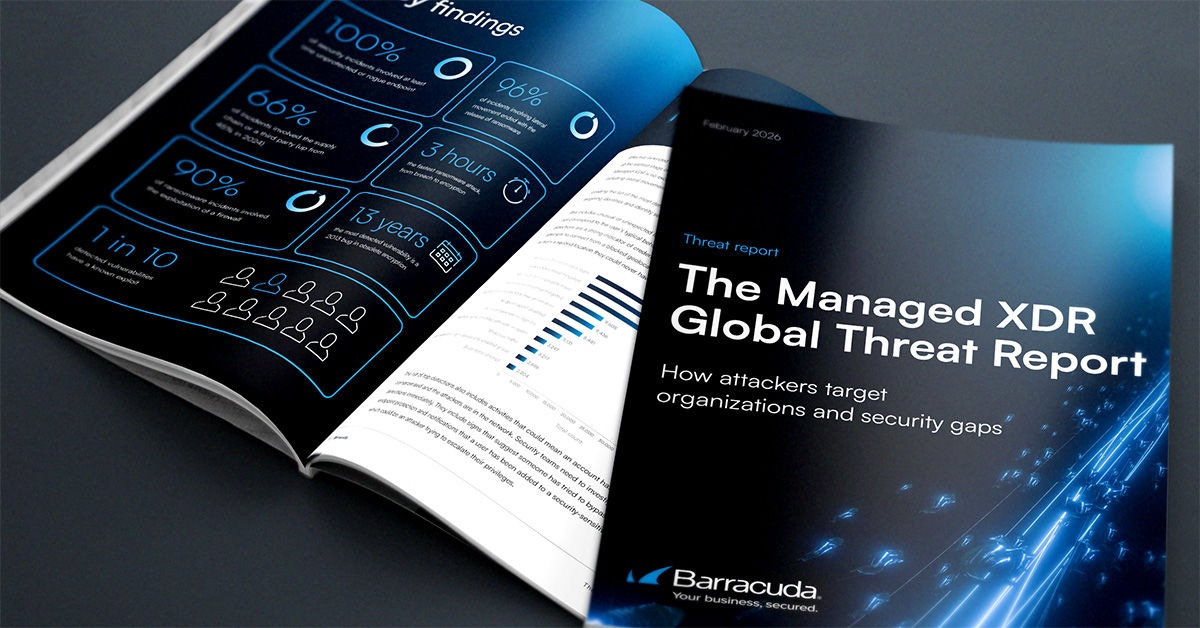
The Managed XDR Global Threat Report
Key findings about the tactics attackers use to target organizations and the security weak spots they try to exploit
Subscribe to the Barracuda Blog.
Sign up to receive threat spotlights, industry commentary, and more.

The Email Security Breach Report 2025
Key findings about the experience and impact of email security breaches on organizations worldwide