AI-Driven Intelligent Login Protection with Barracuda WAF-as-a-Service
How AI-driven discovery and adaptive enforcement close authentication blind spots at scale
Takeaways
- You can’t protect login pages you don’t know exist. AI-driven discovery is now essential to maintain accurate, continuous visibility.
- Precision matters for stopping credential abuse. Extracting the correct action URLs and credential parameters allows protections to target the exact login submission points, dramatically reducing false positives while improving effectiveness against brute force, credential stuffing, and account takeover.
- Automation is the only way to scale authentication security. Generative AI detection, ML-driven policy recommendations, and TTL-governed rescanning eliminate manual tuning overhead and keep protections current as applications and attack techniques evolve.
Thought preface
Login endpoints are the narrowest choke point in an application journey and the most aggressively targeted. Attackers exploit credential stuffing, password spraying, enumeration, reverse-proxy phishing, and stealth automation to bypass defenses. Meanwhile, teams ship microsites, localized flows and embedded logins in fast-moving releases, creating blind spots. The traditional approach of manual discovery, configuration and maintenance of login page protections has become untenable and stolen credentials remain a primary method attackers use to gain initial access -- accounting for roughly 32-33% of breaches in the 2025 Verizon Data Breach Investigations Report (DBIR).
This paper presents Barracuda’s AI-driven Login Page Detection and Protection system — a comprehensive platform that leverages generative AI, advanced machine vision techniques, OCR and machine learning (ML) to automatically discover, analyze and protect login surfaces at scale.
The problem space
The visibility challenge: Unknown attack surface
Modern organizations operate in a state of perpetual uncertainty regarding their authentication landscape:
The questions security teams struggle to answer:
- “Do I have a login page?” – Shadow IT and decentralized development create authentication endpoints without security oversight.
- “Do I have multiple login pages?” – Microservices architectures spawn dozens of independent authentication surfaces.
- “Where are my login pages?” – Dynamic applications, gateways, and third-party integrations obscure visibility.
- “How do I protect them?” – Manual configuration doesn’t scale across distributed, rapidly evolving infrastructures.
The scale of the problem
According to Barracuda Web Application Firewall (WAF)-as-a-Service platform documentation, enterprise organizations typically have:
- 50-500+ web applications across their portfolio
- Multiple authentication mechanisms per application
- Weekly or daily deployments that introduce new login surfaces
- Limited visibility into third-party and partner-managed applications
Evolving attack sophistication
Authentication attacks have become increasingly automated, distributed and difficult to detect:
- Credential stuffing attacks leverage billions of stolen credentials from data breaches: leverage billions of stolen credentials from data breaches:
- 24 billion credentials exposed in 2024 alone
- Automated tools test credentials across thousands of sites
- Success rates of 0.1-2% still yield millions of compromised accounts
- Average breach cost: $4.8 million per incident
- Account takeover (ATO) attacks increased 250% in 2024, with sophisticated techniques
- AI-Powered attack tools increasingly used to automate login page detection and brute-force attacks.
- Credential theft is a key factor in roughly 32-33% of breaches in the 2025 Verizon DBIR
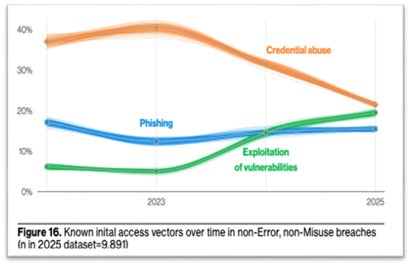
Research from 2025 Verizon Data Breach Investigations Report
Operational constraints:
Many teams lack dedicated IT or site reliability engineering (SRE) capacity. Protections must be accurate, adaptive and low touch to avoid harming conversion.
Industry context:
• OWASP cheat sheets outline credential abuse patterns and mitigations
• NIST SP 800-63B recommends phishing-resistant authenticators and strong lifecycle controls
Vision
The Barracuda WAF-as-a-Service intelligent login protection solution
Barracuda WAF-as-a-Service delivers this vision through an integrated, AI-powered platform:
✅ Automated discovery – AI agents continuously scan applications to identify login surfaces
✅ Multimodal analysis – Advanced machine vision techniques, optical character recognition (OCR) and ML models extract technical details from screenshots and HTML source
✅ Intelligent policy generation – ML models recommend optimal security configurations based on application behaviour
✅ Zero-touch deployment – Automated configuration and enforcement with minimal human intervention
✅ Continuous adaptation – Feedback loops refine detection and protection as threats evolve, A periodic check of stored login page using time to live (TTL) mechanisms to make sure data is up-to-date
Key differentiators:
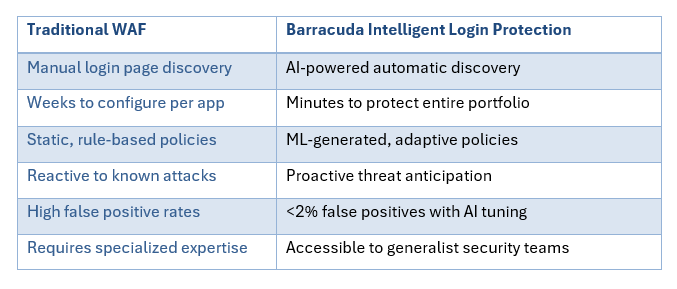
Key differentiators between a traditional WAF and Barracuda Intelligent Login Protection
Architecture and design
High-level components
- Log ingestion & Databricks pipeline: Ingest data ingestion logs into an Event Hub (or equivalent) and process with a Databricks pipeline for streaming extract, transform, and load (ETL), TTL checks, and detection orchestration
- Barracuda Intelligence Service: Applies filter and feeds HTML source, screenshots using in-built tools. Also, it validates TTL and updates metadata databases (metadata DB) accordingly to maintain up to date data.
- Barracuda GenAI Engine: Multi-modal analysis of screenshots and HTML to reliably detect login pages, action URLs, and credential parameters
- Metadata database: Stores URLs, TTL status, detection confidence, features, and lineage for coverage governance
- Barracuda recommendation (Reco) engine + ML: Generates brute-force, credential abuse, and ATO policy recommendations and writes them to Reco DB with full audit
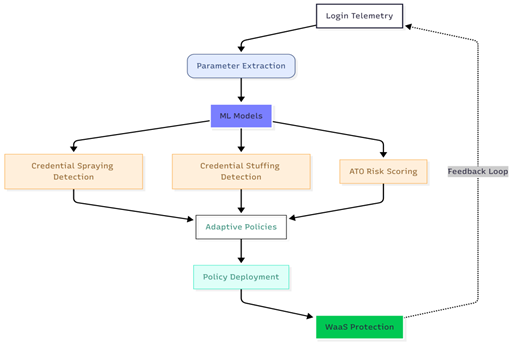
Flow (aligned to architecture diagram):
- Barracuda WAF-as-a-Service sends data ingestion (DI) logs → Event Hub → Databricks pipeline consumes and normalizes.
- Pipeline checks Metadata DB: if URL is new or TTL expired, submit to the Barracuda Intelligence Service for detection.
- Intelligence Service filters and forwards screenshots + HTML to the Barracuda Gen AI Engine for multi-modal analysis.
- If page is classified as a login surface, write login URL to Metadata DB and emit a detection event.
- The Reco engine evaluates action URLs and credential parameters and writes policy recommendations (brute-force, credential abuse, ATO) to Reco database with TTL and audit.
- Barracuda WAF-as-a-Service retrieves and applies approved recommendations, enabling targeted protections with minimal manual effort.
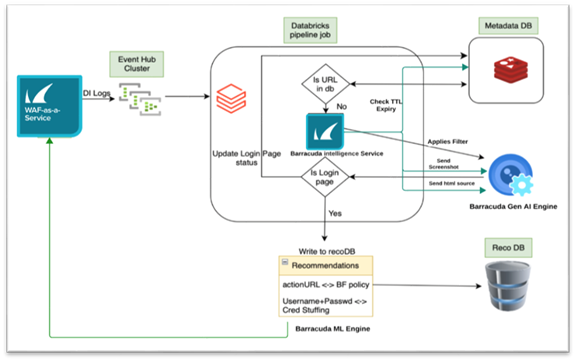
Barracuda WAF-as-a-Service Intelligent Login Protection workflow
- Azure Event Hubs—high-throughput streaming
- Databricks Structured Streaming—scalable pipelines
Innovation layer: What is technically new
- Multi-modal Gen AI detection: Fuses machine vision, OCR techniques on screenshots with semantic HTML analysis to robustly detect login forms across server-rendered UIs, and localized variants.
Comparison to state-of-the-art:
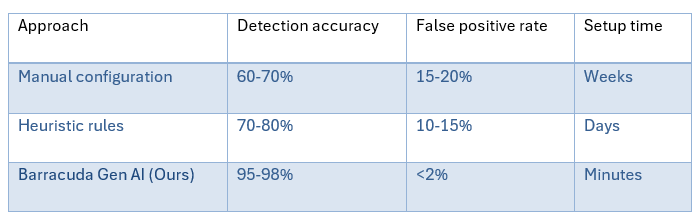
Barracuda WAF-as-a-Service Intelligent Login Protection

Multi-modal GenAI detection in Barracuda Intelligent Login Protection
- Precise action URL and credential parameter extraction: Targets enforcement to the correct submission endpoints and fields.
- TTL-governed rescanning with audit: Rescan cadence that avoids wasteful work while keeping detection current; every recommendation has TTL and lineage for the login page detected.
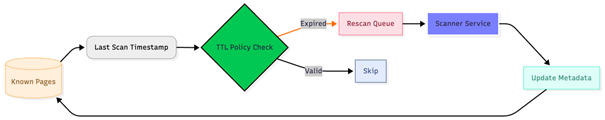
Rescan cadence workflow in Barracuda Intelligent Login Protection
- ML-based policy recommendations: Automated, explainable configurations for
- Brute-force policy recommendations
- Credential spraying / stuffing and ATO
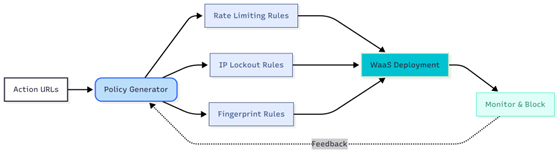
Automated configurations for Brute-force policy recommendations
Automated configurations for credential spraying / stuffing and ATO
• End-to-end automation with zero-touch deployment:
Innovation: Complete automation from discovery to protection
Technical workflow:
- Discover: AI identifies login pages automatically
- Analyze: Gen AI extracts technical details
- Recommend: ML generates optimal policies
- Deploy: Auto-configuration applies protection
- Adapt: Continuous learning refines policies
Real-world application and case studies
Case 1: Multi-brand commerce with unknown login variants
- Challenge: Microsites and localized login forms launched weekly, outpacing manual inventory and protection. Multiple login pages across customer, vendor and admin portals.
- Approach: AI-based discovery is used to populate a central registry. High-churn sections like login detection, action URLs and credential mappings are kept current by TTL-aware rescans.
- Result: Full coverage, onboarding time for protections shortened, brute-force and spraying attempts contained early (see OWASP credential abuse patterns here.).
Case 2: SaaS under reverse-proxy phishing pressure
- Challenge: Session relay via phishing proxies increased ATOs and MFA fatigue.
- Approach: ATO profiling across device, geo-velocity and cookie integrity.
- Result: Phishing-driven ATOs dropped; legitimate login success remained high due to adaptive, low-friction protections.
Case 3: Media network with high automation pressure
- Challenge: Credential stuffing from rotating residential proxies inflated auth workload and hurt conversion.
- Approach: Per-action URL brute-force controls, velocity checks, and credential abuse policies cut attack throughput, TTL avoided unnecessary rescans of stable pages.
- Result: Attack volume curtailed, conversion stabilized, ops workload decreased via automated recommendations.
Broader impact
- Security posture & compliance: Reduced ATO risk and alignment with phishing-resistant authentication options.
- User experience & trust: Adaptive friction and passkeys improve sign-in ease while resisting phish.
- Operational efficiency: AI-driven discovery + ML recommendations reduce manual work, TTL avoids waste and audits simplify governance.
- Scalability: Streaming ingestion (Event Hubs) and structured streaming pipelines (Databricks) handle high-volume telemetry and near-real-time protection.
Key takeaways
- Automatic intelligent discovery: AI agents continuously find and classify login pages across every app, domain, and locale.
- Extract precisely: Map action URLs and credential parameters to target brute-force and credential abuse protections accurately.
- Govern freshness: TTL policies prevent wasteful rescans while keeping detection data current.
- Automate enforcement: Apply ML-driven recommendations for brute-force, spraying/stuffing, and ATO—complete with audit trails and TTL.
- Prefer phishing resistance: Make passkeys/WebAuthn the default step-up for high-risk scenarios to neutralize proxy phishing.
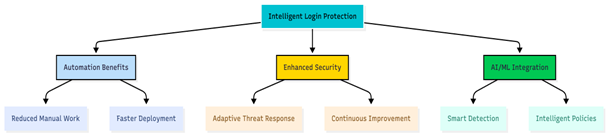
Barracuda Intelligent Login Protection overview
Conclusion: The path forward
The Barracuda Intelligent Login Protection system represents a fundamental shift in how we approach web application security. By combining generative AI, computer vision, machine learning, and automated policy generation, we’ve created a solution that:
✅ Discovers login surfaces automatically across any application portfolio
✅ Analyzes authentication flows with human-level understanding
✅ Protects against credential stuffing, spraying and account takeover at scale
✅ Adapts continuously to new threats and application changes
✅ Scales effortlessly from dozens to thousands of applications
As credential-based attacks continue to surge and the cybersecurity skills gap widens, AI-powered automation is no longer a luxury—it’s a necessity.
The question is no longer whether to adopt AI for security, but how quickly you can deploy it to protect your organization and customers.
The future of authentication security is intelligent, automated, and adaptive. The future is now.
This technical blog post is based on Barracuda’s internal architecture documentation and is intended for security engineers, DevOps professionals, and technical decision-makers
The Managed XDR Global Threat Report
Key findings about the tactics attackers use to target organizations and the security weak spots they try to exploit
Subscribe to the Barracuda Blog.
Sign up to receive threat spotlights, industry commentary, and more.

The Email Security Breach Report 2025
Key findings about the experience and impact of email security breaches on organizations worldwide