
World Backup Day: Is the 3-2-1 backup rule still relevant?
Why SaaS, identity data and OT systems require a modern take on a decades‑old backup framework
Takeaways
- The 3‑2‑1 rule still works — but only if it applies to modern data types. Backups must extend beyond files and databases to include SaaS application data, identity configurations and operational technology systems.
- Redundancy without separation is not resilience. Backing up cloud data inside the same cloud environment creates copies, not protection. Meaningful separation — including cross‑cloud and administrative isolation — is now essential.
- Recoverability matters more than retention. Immutable backups, independent access controls and regular restore testing determine whether data can actually be recovered after ransomware, misconfiguration, or system failure.
The 3-2-1 backup rule is widely attributed to photographer Peter Krogh, who wrote about the importance of data protection in his book on digital asset management. Krogh didn’t invent the concept; he just coined the phrase. The idea was later formally credited to him in a 2012 US-CERT publication on data backup options.
At the time, 3-2-1 provided a simple, reliable framework for protecting data in on-premises environments. But the infrastructure assumptions it was built on no longer reflect how most organizations operate. Production data now lives across SaaS platforms, identity systems, cloud services, and operational technology (OT) environments. The rule itself isn’t broken — but the way many organizations apply it hasn’t kept up.
“Anything you have on only one hard drive is a thing you don’t mind losing today.” ~ Peter Krogh
What the original 3-2-1 rule was designed to solve
The original 3-2-1 rule looks like this:
3 – Keep three copies of any important file: one production copy and two backups.
2 – Store backups on two different media types to protect against different failure modes.
1 – Keep one copy offsite, away from the primary production environment.
This approach was designed for physical infrastructure. Production servers lived in a data center or a server room at the office. Backups were written to tape or disk. Offsite storage meant physical separation. The goal was resilience through redundancy and distance.
Over time, variations emerged. Some emphasized keeping two backup copies rather than two media types. Others replaced physical separation with cloud storage. The framework gradually shifted away from the literal “3-2-1” checklist and toward a broader question: do you actually have independent, recoverable copies of your data?
How the industry already evolved 3-2-1
The first major evolution was the 3-2-1-1 rule, which added a requirement that one backup copy be immutable or air-gapped. This change was a direct response to ransomware.
If an attacker can encrypt your production systems and your backups using the same credentials, you don’t have a backup — you have a second target. Immutability, whether implemented through write-once storage, cloud isolation, or physical separation, ensures at least one copy of data survives an attack.
The next evolution, 3-2-1-1-0, addressed a quieter but equally damaging problem: untested backups. The “zero” refers to zero errors in backup verification and recovery testing. No one wants to discover that their backups have corrupt or missing data after an incident. The zero reminds us that backup success is measured at restore time, not backup time.
Why 3-2-1 breaks down in SaaS environments
The first major pressure point for 3-2-1 is software-as-a-service (SaaS).
When production data lives in a SaaS platform like Microsoft 365, the idea of “offsite” can be misleading. The data already lives in someone else’s data center, outside the physical risks of the business location. SaaS providers deliver redundancy and availability to keep services running, but those controls have nothing to do with data backup.
Microsoft is explicit about this shared responsibility model: customers own their data and identities and are responsible for protecting them. Retention policies and recycle bins offer limited, short-term recovery, not true backup or disaster recovery.
You could create backups of your data in the same cloud environment, such as an Azure-hosted backup for Azure-hosted production data. This gives you a second copy of the data, but it might not provide meaningful separation. A tenant-level compromise, credential theft or cloud-wide incident can affect both your production copy and the backup.
For SaaS, the modern 3-2-1 adaptation is cross-cloud air gapping. Backups must live in a separate administrative domain, with independent credentials and access controls. A third copy might live on premises or in a separate cloud account entirely. The goal is not just redundancy, but independence. If Microsoft or an administrator account is compromised, recovery must still be possible.
Identity infrastructure: the data most organizations forget
When it comes to data backup, most IT teams are thinking about files, email systems, databases, etc. Identity infrastructure is not always on that list.
Systems like Microsoft Entra ID contain the data that determines who can sign in, what they can access and how authentication works across the environment. Users, groups, roles, app registrations, conditional access policies, and authentication methods all live there. Losing or corrupting this data means losing control of the environment itself.
Many companies overlook identity configurations as a data class. They aren’t included in backup policies, rarely have defined retention periods, and are often excluded from recovery testing. Native recovery options are limited, and there is no built-in way to roll back many critical configuration changes. For many companies, there is only one copy of identity data stored in production.
A modern 3-2-1 strategy treats identity infrastructure as mission-critical data with its own backup cadence, retention requirements and restore testing. Identity changes constantly. Traditional file and email backups do not protect it.
Operational technology: rethinking what counts as “data”
Operational technology environments present a different challenge. The question isn’t where backups live — it’s what data is worth backing up at all.
In OT, critical data includes controller logic, firmware, device configurations, and network segmentation rules that keep industrial processes working safely. Losing that data can cause downtime and compromise the safety of workers or the public.
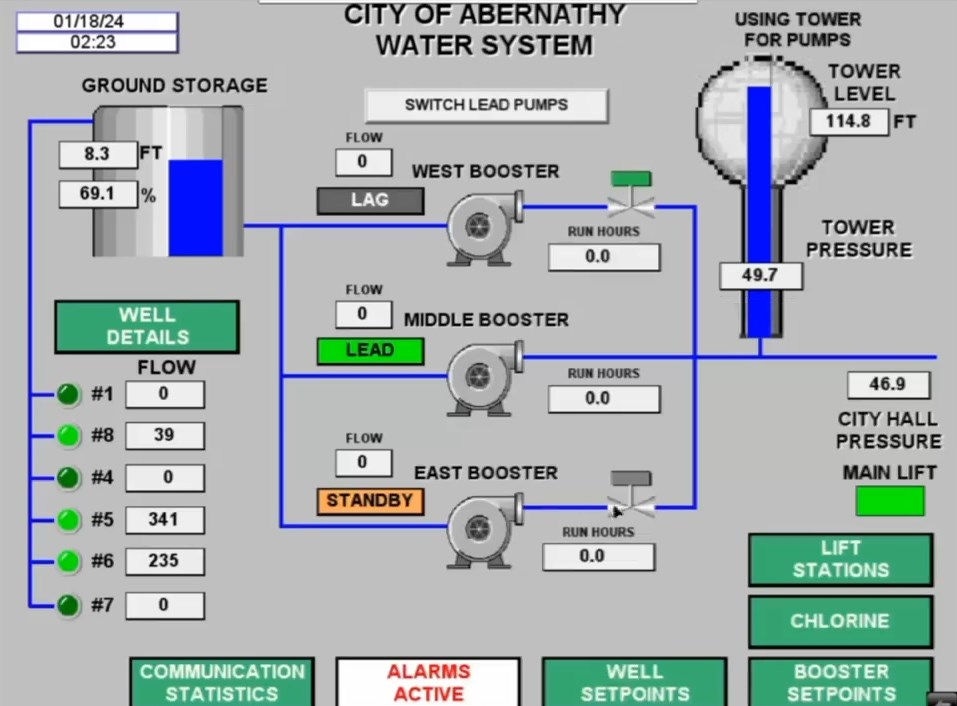
Threat actors demonstrated they had access to water control systems in Abernathy, Texas
OT backups are complicated by proprietary formats, safety concerns and the inability to regularly test restores without disrupting production. Even when backups exist, organizations may rely on documentation or manual rebuilds as recovery mechanisms.
Here, the 3-2-1 adaptation is about expanding the definition of critical data. Frameworks like IEC 62443 help organizations identify and classify OT assets, define ownership, and align backup and recovery practices with safety and risk requirements. The principle remains the same: if the data is required to recover operations, it must be protected.
The 3-2-1 rule still works — if you ask the right questions
The 3-2-1 rule persists because its principles are sound. Redundancy, separation and independence still protect data against most loss scenarios. What has changed is the landscape those principles must cover.
For World Backup Day 2026, the most important questions are no longer about storage media or locations, but about coverage and recoverability:
- Are you backing up everything? Not just files and email, but SaaS application data, identity configurations and OT assets.
- Are your backups truly separated from production? Backing up cloud data within the same cloud is duplication, not isolation.
- Are you treating identity as a data class? If Entra ID isn’t recoverable, neither is the environment it controls.
- Are your backups immutable? If ransomware can reach them, they are targets, not safeguards.
- Have you tested a restore recently? Recoverability only exists if it’s been proven.
The 3-2-1 rule helps organizations think clearly about resilience, and it’s flexible enough to adapt to the infrastructure you are using today. If you haven’t thought about your backup strategy in a while, consider the 3-2-1 rule as it applies to all your data – identity, OT, webhooks and custom integrations, security tooling like trigger rules and endpoint protection configurations.
The Center for Internet Security (CIS) Controls 3 and 11 cover data protection and recovery. We’ve summarized these controls in our post here. These CIS Controls can help you identify and protect the data in your environment.
Barracuda offers data protection solutions designed to support these backup requirements. For more information on how we can help protect your data, see the following resources:
- Barracuda Cloud-to-Cloud Backup — SaaS backup and recovery for Microsoft 365
- Barracuda Entra ID Backup Premium — Comprehensive backup for all 13 critical Entra ID components
- Barracuda Backup — On-premises and cloud backup for physical, virtual, and cloud environments
- Defense-in-depth strategies to protect critical Entra ID data – On demand webinar on protecting business-critical Entra ID data.
The Managed XDR Global Threat Report
Key findings about the tactics attackers use to target organizations and the security weak spots they try to exploit
Subscribe to the Barracuda Blog.
Sign up to receive threat spotlights, industry commentary, and more.

The Email Security Breach Report 2025
Key findings about the experience and impact of email security breaches on organizations worldwide





