
Have your say: NIST seeks feedback on draft cybersecurity framework for transit
How transit agencies can shape robust cyber defenses with NIST’s latest guidance
Takeaways
- Cyberattacks targeting transit and transportation systems are increasing in frequency and impact, raising the stakes for cybersecurity across the sector.
- NIST has released a draft Transit Cybersecurity Framework Community Profile to help transit agencies manage cyber risk in a practical, sector‑specific way.
- The draft framework is voluntary, risk‑based and aligned with NIST Cybersecurity Framework 2.0, while accounting for transit‑specific operational realities.
- NIST is actively seeking feedback from transit IT and security professionals to ensure the framework reflects real‑world challenges.
- Comments are due by February 23, 2026, making this a timely opportunity for the transit community to help shape future guidance.
Transit systems never stop moving, and neither do cyberthreats. The National Institute for Standards and Technology’s (NIST’s) newly released draft cybersecurity framework for transit agencies is open for public comment, and the people who run and secure these systems have a chance to help shape what comes next.
Cybersecurity: A growing concern for transit agencies
Public transportation systems are increasingly attractive targets for cybercriminals. And the consequences of a successful attack can extend far beyond IT disruption. As transit agencies adopt more connected technologies, integrate operational technology (OT) with IT systems and rely on digital tools to manage daily operations, their attack surfaces continue to expand.
Industry reporting (e.g., here, and here) shows that cyberattacks across the broader transportation sector have risen steadily in recent years, with ransomware, phishing and distributed denial‑of‑service (DDoS) attacks among the most common threats. Rail, aviation, maritime, and public transit systems have all experienced incidents that disrupted services, exposed sensitive data or forced organizations to revert to manual processes. In some cases, attacks on transportation organizations have caused service outages that directly impacted passengers and freight movement, underscoring the sector’s role as critical infrastructure.
These risks are compounded by legacy systems, safety‑critical operations, wireless connectivity requirements, and the need to keep systems running continuously. For many transit agencies, cybersecurity isn’t just an IT issue. It’s a matter of public safety, service reliability and operational resilience.
NIST’s draft framework for the transit community
To help address these challenges, NIST has released an initial public draft of the Transit Cybersecurity Framework Community Profile (NIST IR 8576). Developed by NIST’s National Cybersecurity Center of Excellence (NCCoE), the draft is intended specifically for U.S.‑based transit agencies and operators.
The framework is voluntary and non‑regulatory, designed to complement rather than replace existing cybersecurity programs. It builds on NIST Cybersecurity Framework 2.0, translating its core outcomes into guidance that reflects the operational realities of transit environments, including buses, rail systems, subways, and commuter services.
Rather than prescribing a one‑size‑fits‑all approach, the draft profile is meant to be adaptable. NIST emphasizes that agencies of different sizes and maturity levels should be able to tailor the guidance to their specific risks, resources and mission priorities.
An overview of the recommendations
At a high level, the draft Transit Cybersecurity Framework Community Profile focuses on helping agencies:
- Identify and prioritize cybersecurity outcomes that align with transit‑specific mission needs, such as passenger safety and service continuity
- Manage risk across both IT and OT systems, recognizing the interdependence between digital infrastructure and physical operations
- Improve communication and collaboration around cybersecurity risk within agencies and with external partners, suppliers and stakeholders
- Scale cybersecurity efforts based on organizational size, complexity and risk tolerance
The draft also highlights certain cybersecurity outcomes as “elevated” for the transit sector, reflecting their importance in protecting safety‑critical and always‑on systems. NIST is explicitly seeking feedback on whether these priorities and designations resonate with real‑world transit operations.
One theme that runs consistently through the draft framework is cyber resilience — the ability not just to prevent attacks, but to continue operating safely and recover quickly when incidents occur. For transit agencies, that’s especially important given always‑on services, safety‑critical systems and limited tolerance for downtime.
At the same time, many transit agencies are working with small, overstretched IT and security teams that are expected to manage everything from legacy infrastructure to modern threat detection. This reality makes it difficult to maintain 24/7 monitoring, investigate alerts and respond to incidents quickly, particularly as attacks grow more frequent and more sophisticated.
For some organizations, this is where an outsourced security operations center (SOC) and extended detection and response (XDR) services such as Barracuda Managed XDR can play a supporting role. By augmenting internal teams with continuous monitoring, threat detection across endpoints, networks and cloud environments, and guided incident response, transit agencies can strengthen resilience without adding operational burden. Approaches like these align well with the framework’s emphasis on scalable, risk‑based cybersecurity outcomes rather than one‑size‑fits‑all solutions.
Your feedback matters — what to do next
NIST is actively soliciting input from transit IT, security and operational professionals to ensure the final framework reflects the realities agencies face every day. This includes feedback on clarity, usability, prioritization, and how agencies expect to apply the guidance in practice.
If you work in cybersecurity, IT or risk management within the transit or transportation sector, now is the time to review the draft and share your perspective. The public comment period is open through February 23, 2026, and stakeholder input will directly influence the final version of the framework.
For a sector where systems never stop moving, shaping practical, effective cybersecurity guidance is a shared responsibility. Don’t miss this opportunity to help strengthen cyber resilience across the transit community.
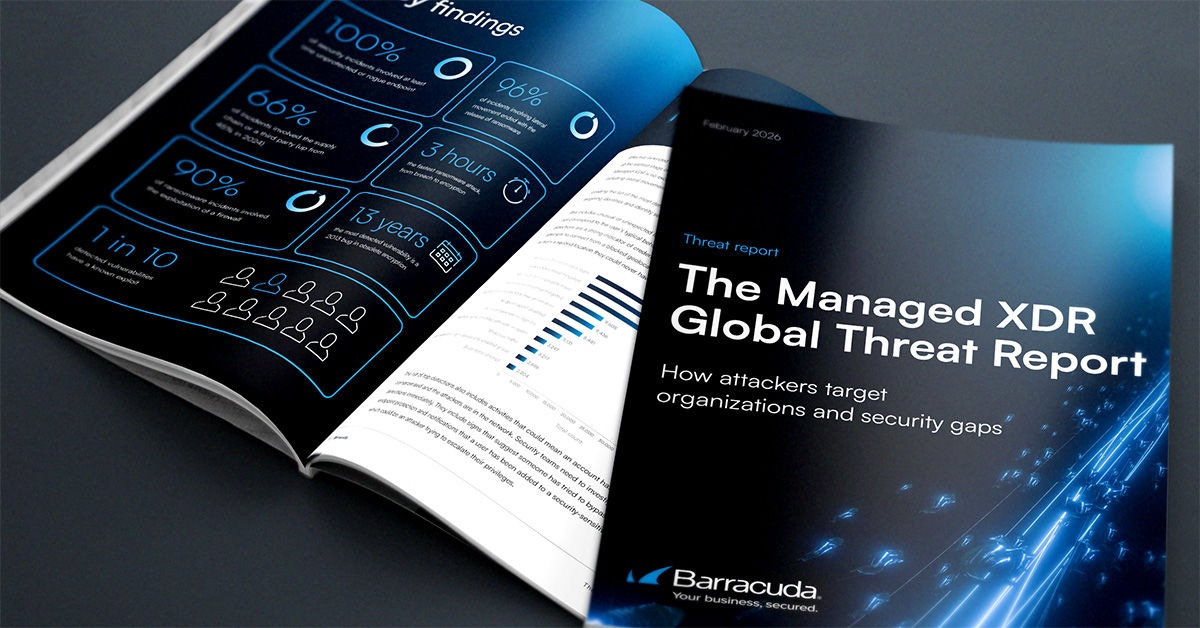
The Managed XDR Global Threat Report
Key findings about the tactics attackers use to target organizations and the security weak spots they try to exploit
Subscribe to the Barracuda Blog.
Sign up to receive threat spotlights, industry commentary, and more.

The Email Security Breach Report 2025
Key findings about the experience and impact of email security breaches on organizations worldwide





