Why is it important to report cybercrime?
Many countries, plus all 50 U.S. states, require companies to report data breaches that put personally identifiable information (PII) at risk. Failure to do so risks severe penalties. Under the GDPR, for example, companies that don’t report data breaches can receive fines of up to €10 million or 2% of global yearly revenue, whichever is greater. But reporting data breaches should be motivated by something other than fear.
Let’s say that you experience a data breach that doesn’t quite rise to the reporting threshold. The ransomware attack infects a single server with nothing important on it, so you wipe and reimage. You find a Trojan on an endpoint before it can exfiltrate any data. These attacks can be seen as trivial, but they’re still absolutely worth reporting. In the war against cybercrime, all data points are important.
Ransomware groups are stealthy — so every clue is important
Attackers have become very good at covering their tracks during and after a successful cyberattack. While the attack is in progress, infected computers will communicate with attackers using hidden communications called command and control (C2).
C2 often involves disguising malicious traffic as ordinary application traffic. Malware can also escape detection by using uncommon high-numbered ports. Beaconing is another way to avoid detection in which malware will broadcast requests for instructions at random intervals, often hours or days after the initial infection has been accomplished.
By disguising traffic and moving slowly, sophisticated attackers can evade heuristics, IDS/IPS and other forms of defense. Instead of attracting attention with a flurry of activity, the malware remains below the threshold of detection. Once the attack has been accomplished, the malware wipes or encrypts itself, erasing the evidence.
This combination of techniques means that malware groups can be very difficult to track down — and if they make mistakes, it becomes essential for investigators to receive the evidence.
Every threat actor leaves traceable information
The most successful ransomware groups and advanced persistent threats (APTs) can operate for years at a stretch. The LockBit group, for example, ran from 2019 to 2024 before it was dismantled. The ransomware group currently known as BlackSuit has been operating under one name or another since 2016, when they began offering the Hermes ransomware. Some APT groups, which are usually state-sponsored, have run for over a decade.
When groups like this operate for a long time, they develop habits. BlackSuit will often gain entry by using a phishing email that installs a remote access Trojan called SystemBC. They’ll use Cobalt Strike and Mimikatz, plus more legitimate tools like PowerShell and PSExec, to spread, persist and escalate privileges. Finally, they use a partial encryption strategy to encrypt more files faster before they start tripping detection thresholds.
Why do failed attacks become clues for law enforcement?
Now, let’s say that you’re a CISO or a security analyst. You discover one of your endpoints has been infected by SystemBC while it’s in the process of beaconing to a C2 server. You do the right thing and send your logs to an investigator. From this information, the investigator takes the use of SystemBC as a good sign they’re dealing with BlackSuit. Now they know the address of a BlackSuit C2 server.
Does BlackSuit immediately understand that their intrusion attempt has failed? Maybe not. Do they immediately shut down their C2 server after a failed intrusion? Maybe not. If the server is still active, the investigator can potentially locate it to a physical data center and learn who’s renting it. If they combine the information they’ve learned with information from other investigators, they can potentially shut down the group’s servers and make arrests.
By the way, the example above is barely fiction. On July 24, 2025, a joint task force of U.S. and European law enforcement seized BlackSuit domains and infrastructure, recovering data that will likely unmask the group’s members. Tips like the one above aren’t just useful in theory. They can genuinely have real-life implications that shut down cybercrime.
How to report a cyber incident (of any scale)
Reports of cyber incidents can start local and end up global. Believe it or not, your local police department is usually the first step in the reporting process when reporting a cyber incident. More and more often, these organizations will have in-house investigators that specialize in cybercrime. They’ll be able to take a report and make referrals to state and federal agencies when necessary.
Alternatively, the Internet Crime Complaint Center (IC3) is a resource comprised of a partnership between the U.S. Department of Justice and the Federal Bureau of Investigation. They’ll be able to review your case and refer to local law enforcement, state or federal agencies or even international agencies when necessary.
If you’re located in the EU, you’ll likely end up dealing with a cybercrime department specific to your member state. For larger-scale incidents, Europol operates the European Cybercrime Center (EC3). This department gathers information about various bad actors and helps coordinate activities between EU states. They also offer emergency technical assistance to help remediate high-profile incidents.
Remember, even if an incident is relatively small and the incident report goes no further than your local police department, that information is still available for review by international investigators. The smallest hint can become instrumental in taking down large and dangerous organizations.
Minimize intrusion risks with Barracuda
There’s a difference between “not reporting cyber incidents” and “not having any cyber incidents to report.” Barracuda offers complete cybersecurity as a service, helping you protect your endpoints, detect vulnerabilities in real time and augment your IT resources. Learn about Barracuda Managed XDR and how we can help your accelerate your detection and mitigation timeline from days to hours — dramatically reducing the risk of enduring a reportable cyber incident.
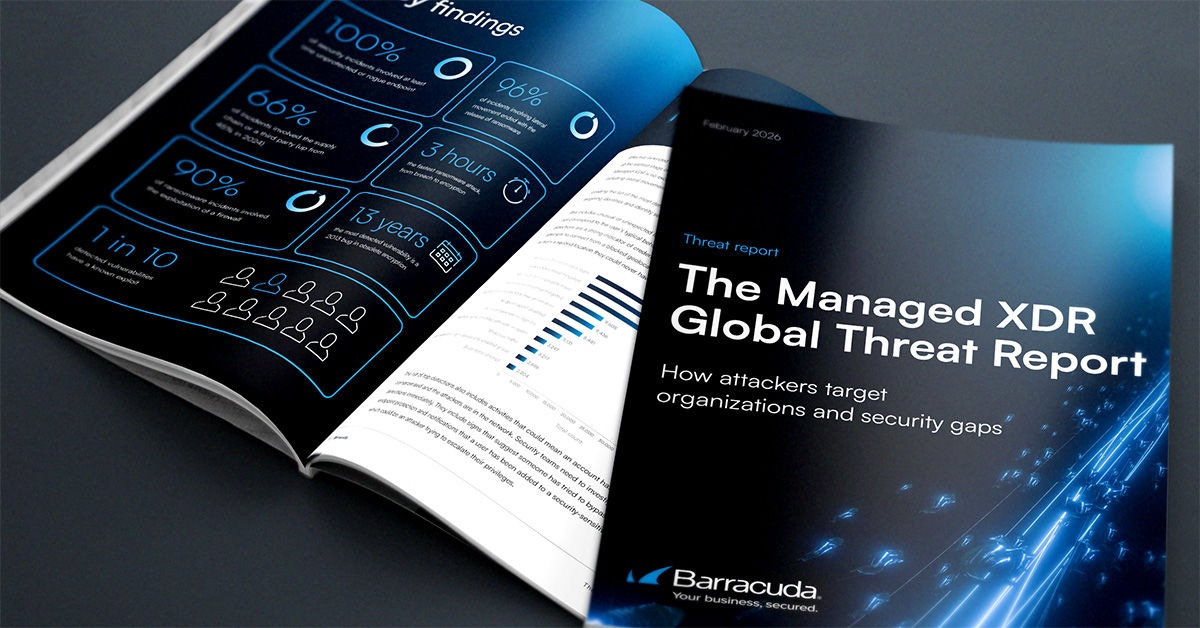
The Managed XDR Global Threat Report
Key findings about the tactics attackers use to target organizations and the security weak spots they try to exploit
Subscribe to the Barracuda Blog.
Sign up to receive threat spotlights, industry commentary, and more.

The Email Security Breach Report 2025
Key findings about the experience and impact of email security breaches on organizations worldwide